Nick Arnott
Latest articles by Nick Arnott

Sparkle updater vulnerability: What you need to know!
By Rene Ritchie, Nick Arnott last updated
Third-party update service Sparkle, combined with insecure network protocols and parsing, leaves some OS X apps open to person-in-the-middle exploits.

What's really going on with the Starbucks mobile app information leak, and what you need to know
By Nick Arnott last updated

Spark Inspector review: Audacious real-time debugging for iOS that might just be too audacious
By Nick Arnott last updated

Locking down iOS 8: How Apple is keeping your iPhone and iPad safe!
By Nick Arnott last updated

Is iMessage secure? The good, the bad, and the complicated
By Nick Arnott last updated

Jekyll apps: How they attack iOS security and what you need to know about them
By Nick Arnott published

Researchers sneak 'Jekyll app' malware into App Store, exploit their own code
By Nick Arnott published
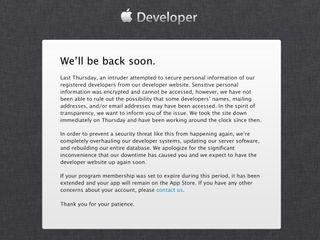
Ibrahim Balic on what he did, why he feels reponsible for Developer Center downtime, and what he's heard back from Apple since
By Nick Arnott last updated

Facebook Blast: Threaded group chat could be coming soon to Messenger app
By Nick Arnott last updated

What the DEA really said about iMessages, and what it means to you
By Nick Arnott published
MOST READ