Fooling Touch ID is anything but trivial, says security boffin
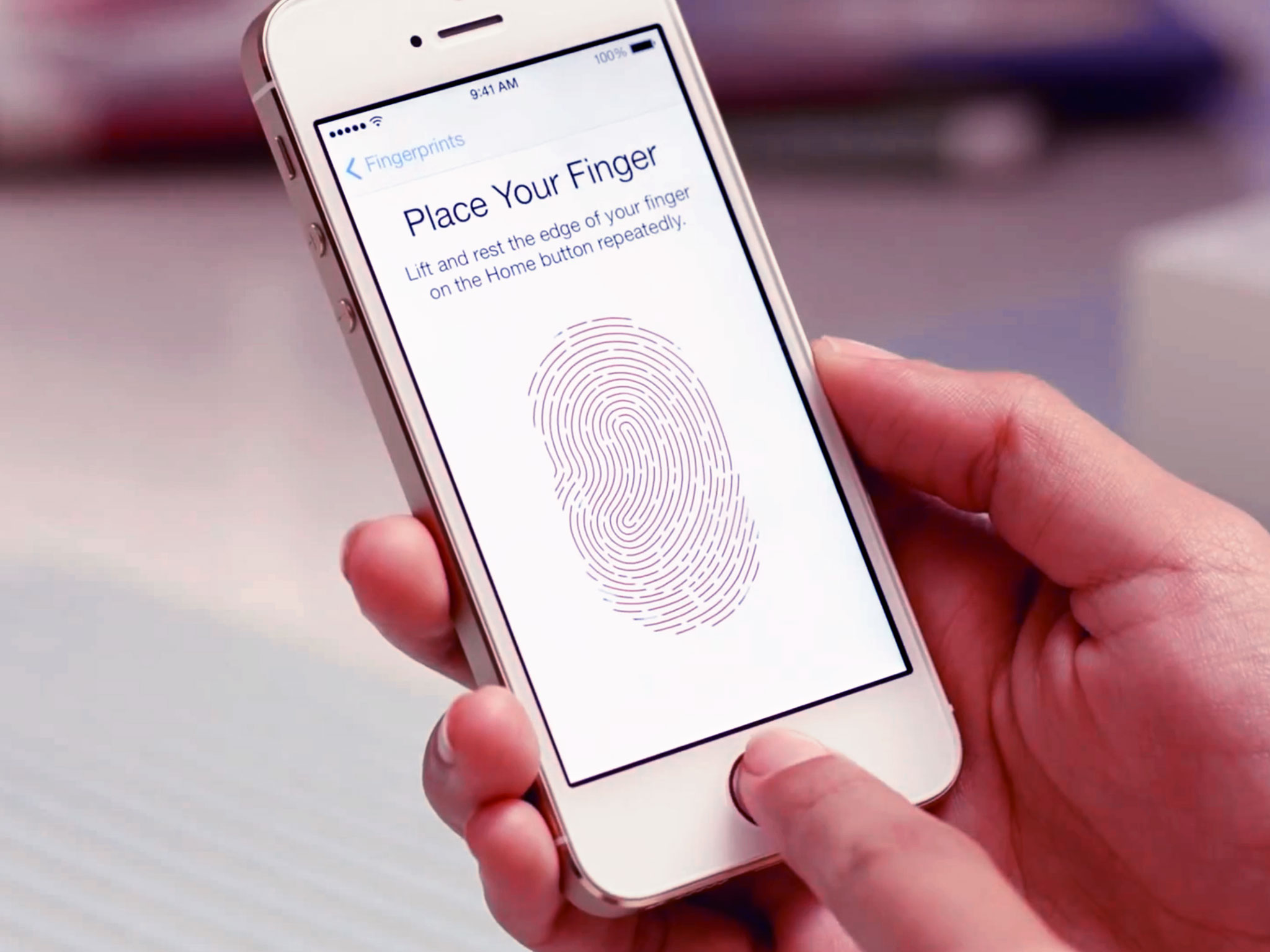
German hacker collective the Chaos Computer Club (CCC) grabbed headlines after showing a method to fool the iPhone 5s's Touch ID fingerprint scanner, but it's nothing that ordinary people need to worry about too much, according to a security expert.
CCC hacker Starbug created a fake fingerprint by scanning a real one, printing it and ultimately creating a fake print by transferring it to latex rubber or wood glue. The group claims that this is proof that biometric security isn't effective and shouldn't be used. Starbug calls his method "very straightforward and trivial."
Security expert Marc Rogers - director of security operations at the DEF CON hacking conference and principal security researcher for mobile security software developer Lookout - posted an entry to the Lookout blog entitled Why I Hacked Apple’s TouchID, And Still Think It Is Awesome. Rogers explains:
Hacking TouchID relies upon a combination of skills, existing academic research and the patience of a Crime Scene Technician.
He talks about some of the issues involved in acquiring an unsmudged print and transferring it. Contrary to Starbug's claims of triviality, Rogers says:
It is a lengthy process that takes several hours and uses over a thousand dollars worth of equipment including a high resolution camera and laser printer.
Rogers underscores that Touch ID is useful as a convenience factor, not as an improved method of security.
Today just over 50 percent of users have a PIN on their smartphones at all, and the number one reason people give for not using the PIN is that it’s inconvenient. TouchID is strong enough to protect users from casual or opportunistic attackers (with one concern I will cover later on) and it is substantially better than nothing.
Rogers also says that Touch ID would be improved if it were a two-factor authentication system - something you have (in this case, your fingerprint) and something you know - a PIN number or passcode. You can't install Touch ID without putting a passcode on your iPhone 5s as well, so the parts are there, if Apple's willing and able.
Over the years a number of studies have been done on smartphone security. And while the number of smartphones in use, and the variety of operating systems in use has increased, the number of users who protect their devices with a lock code or passcode has stayed within a few digits of 50 percent.
iMore offers spot-on advice and guidance from our team of experts, with decades of Apple device experience to lean on. Learn more with iMore!
As Rogers points out, the number one reason why smartphone users don't use a passcode is because they're inconvenient. Touch ID handily addresses the convenience problem. While biometric security isn't perfect, no security is perfect.
If Touch ID's lasting contribution will be to provide that other 50 percent with a viable method of locking and unlocking their phone, Apple will have made a really positive contribution to the smartphone market.
What do you think? Is Rogers understating the risk to Touch ID users? Has Chaos Computer Club overstated how easy Touch ID is to override? I want to hear from you, so share your thoughts in the comments.
Source: MacRumors


