iOS 7: What it means for Enterprise, Education, and Government

Complete breakdown and analysis of Apple's new iOS 7 mobile operating system and what it means for Enterprise, Education, and Government
With iOS 7 Apple has taken their existing support for Enterprise, Education, and Government to the next level, adding even more functionality and better iPhone and iPad device management. This follows years of Apple adding more and more features that allow IT administrators to have more control over iOS devices. iOS obeys all Exchange ActiveSync policies plus it can be further controlled and configured via iOS Configuration Profiles that allow administrators to pre-setup connections to your company's email system for example, or to pre-setup connections to your company's secure Wi-Fi networks, but also restrict the device in many ways including preventing access to the iTunes App Store, or the Safari browser. These are just two examples but the list is quite long.
This has always made iOS devices much more attractive in the enterprise and other platforms like Android have not been adopted because of their lack of support of all ActiveSync policies, but also because there are no ways of restricting apps or pre-setting up things like email or Wi-Fi, amongst other things.
iOS has also provided what are called Mobile Device Management (MDM) Application Programming Interfaces (APIs) that allow MDM vendors like Air-Watch or MobileIron (to name just two) to securely query and control iOS devices.
Lets take a look at the new management features found in iOS 7.
Managing Apps with iOS 7
In iOS 6, through the use of MDM APIs you could:
- Install Apps via MDM. This feature tells the user that they must install an app. The user could ignore this message and the administrator will have to decide how to handle this. They could set the MDM system to automatically lock their device out until they install the app. They could keep calling the user asking them to install the app. Either way, the app cannot be installed for the user by the IT team.
- Delete the app and its data. In much the same way as the app install, the user can only be told they must remove the app. If they don't action can be taken including locking them out of corporate access.
- Prevent app from backing up to the iCloud. This prevents an app you have deployed to a device from backing up its data to iCloud.
With iOS 7 the following has been added:
- Silent app installation. Now via the MDM API, an IT administrator can send an app to the device and have it installed silently in the background. There is no need to ask the user which delays compliance, the app just installs itself. This works both for apps in the iTunes App Store that the company may have purchased a volume license for and apps developed by the company itself for internal use, that are not stored in the iTunes App Store.
- App configurations. This is a very powerful feature that allows an app to receive configuration updates. This could be any configuration information like a URL that the app currently uses for example. The IT administrator can send this configuration update to the app and the app ingests it immediately and from that point onwards has different behavior. Those of you familiar with the old BlackBerry Enterprise Server (BES) may remember that corporate BlackBerry apps can also be configured in a very similar way by adding extra configuration strings to the IT Policy.
- App feedback. Another very powerful feature allows an app to report back, or provide feedback to the MDM system. This could be anything the developer wants to send like errors the app is encountering for example. Allowing the app to provide feedback will certainly cut down on app troubleshooting and even help desk call lengths as companies will now have visibility into the app on a user's iOS device. The MDM system can then make the feedback available in a secondary system to be consumed by that system.
- Managed "Open In". When you choose to open a file (like an attachment) or share a URL or file, you are presented with the Share Sheet that lists all apps that can deal with that file type. With Managed Open In, an IT administrator can, via an MDM system, limit the list of apps that are presented to the user on the Share Sheet. This allows a company to ensure that all data that is stored in corporate apps cannot leak out through an inadvertent sharing to public systems or apps not controlled by the company.Managed Open In can be applied to apps and managed accounts meaning that if you are using your companies email account and want to open an attachment, the list of apps to use is restricted, but if you are using your personal account (like Gmail, Outlook, Yahoo!, etc., the list of apps will be unrestricted).
- Control which apps use cellular data. iOS 7 brings that ability, via an MDM command, to specify which apps can use cellular data. You can imagine how useful this can be for an organization who wants more control over data usage on company provided iOS devices.
- Extra Accessibility Options for Single App Mode. Interestingly for a while now iOS has supported the ability for you to set the device to Single App Mode. This forces the device to only run a certain app no matter if the device is rebooted or the user presses the Home button. iOS 7 brings more control to how this app behaves and more importantly, allows an app to request Single-App Mode, and then later request to exit that mode. Through an MDM setting, you can decide which apps can request Single App Mode. Single App Mode is a good solution for situations like exam taking, kiosks, Point of Sale apps, etc.
Single Sign On (SSO) in iOS 7
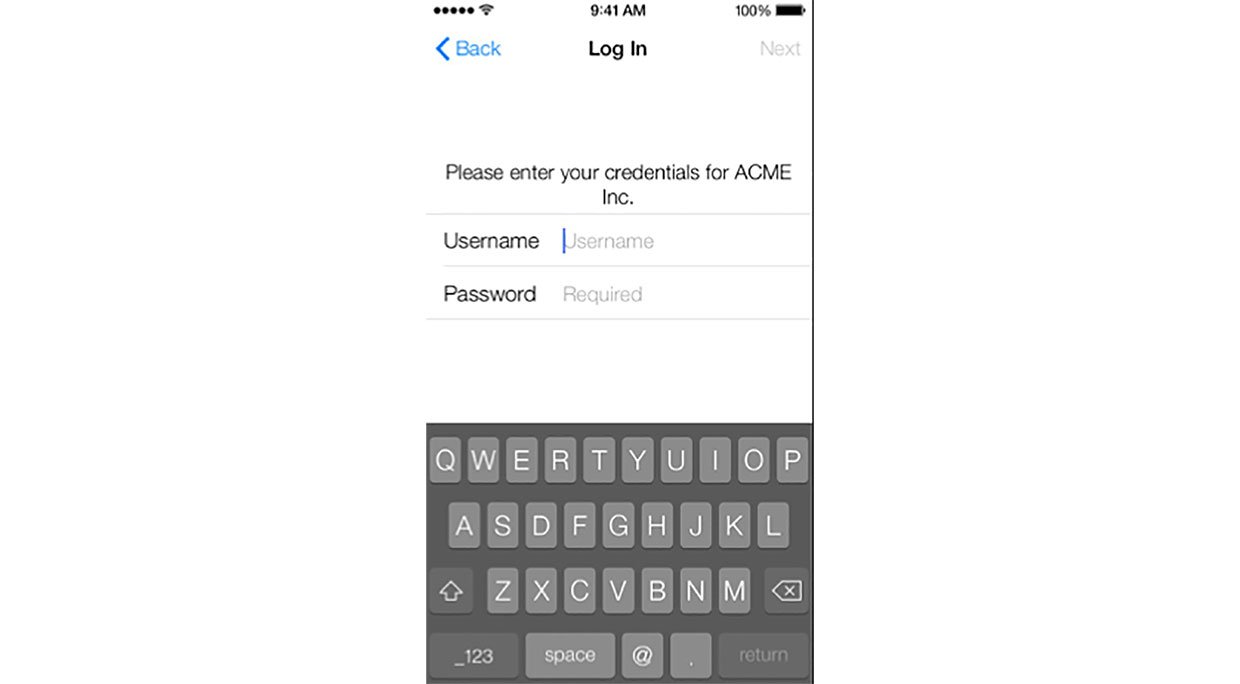
In previous version of iOS, apps written by the same vendor could share login information allowing a user to login only once into one of the apps, and then be automatically logged into other apps by the same vendor. In iOS 7, this can now be done for any app. This means that via MDM, an IT administrator can allow one or more apps to share a common set of login credentials. This is not restricted to apps built by the same vendor, but any apps that the IT administrator assigns.
iMore offers spot-on advice and guidance from our team of experts, with decades of Apple device experience to lean on. Learn more with iMore!

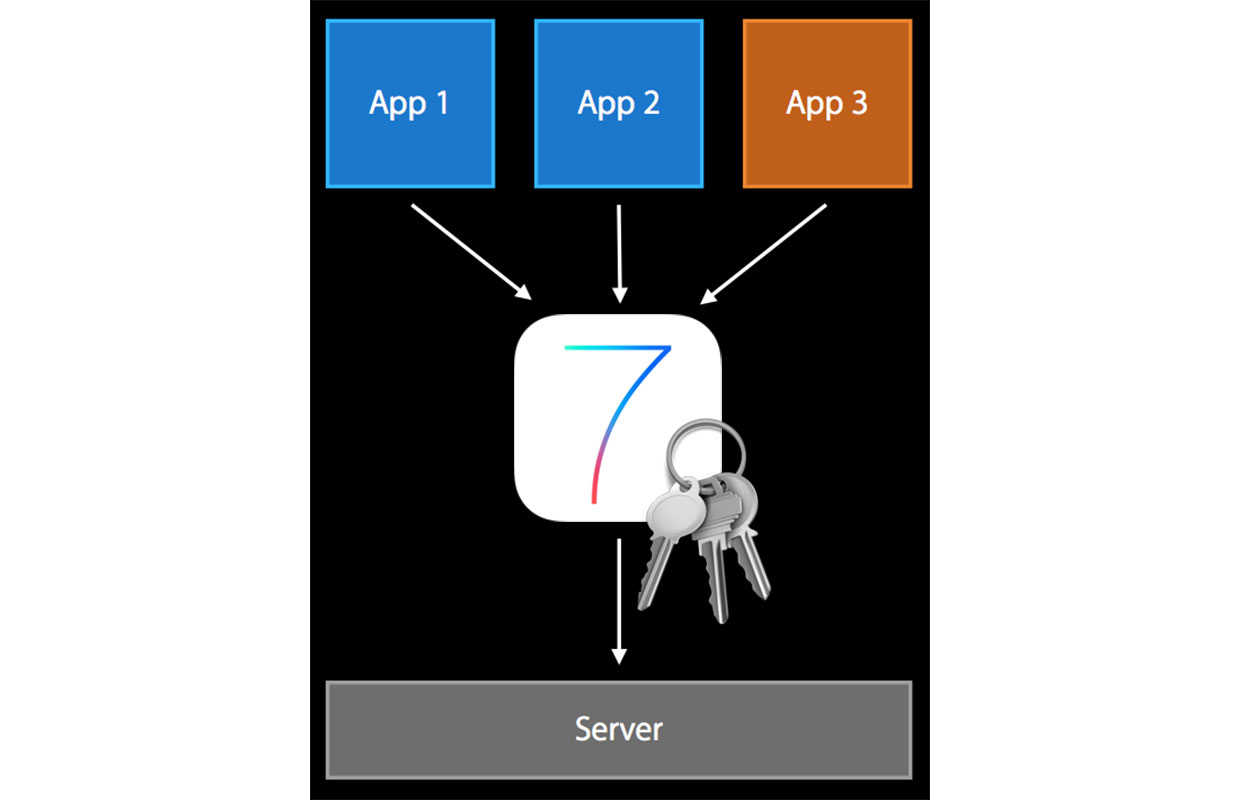
SSO supports a group of apps, and a group of URL prefixes. Supporting URL prefixes allows an enterprise to tell an iOS device that if the user (or an app) browses to a URL that starts with a common phrase (e.g. https://iMore.com/thisisprivate) then the SSO information must be passed to the web server.
Improved Apple Store Volume Purchasing Program (VPP) in iOS 7
Today an enterprise can make volume purchases of an app using a special VPP portal. Once an app is purchased, the enterprise is provided with codes that allow the app to be installed on multiple devices (one code per device). MDM vendors try and make this a bit easier by managing the code assignments and revocations themselves but remember that since an app cannot be uninstalled remotely, revoking the code just means that the app is now not legally allowed to be on a device.
In iOS 7, codes have been replaced by licenses. MDM vendors have been given new APIs to interact with a companies VPP portal and manage the installing and revoking of apps. When an app is revoked, the user is notified that they have 30 days to purchase the app themselves. If they don't, the app will simply stop opening after 30 days making it useless.
IT Administrators can purchase volume licenses for apps and books.
Per-App Virtual Private Network (VPN) in iOS 7
Today on an IOS device, the IT administrator can pre-configure a VPN so that when you start up apps that need access to company data, the VPN provides that secure tunnel into the organization. The problem with this approach is that the VPN is available to any app on the device. This allows personal and private data to be sent via your company's network (which normally means that the apps will break because the company blocks many sites that are considered personal) which could expose your companies data to a rogue app.
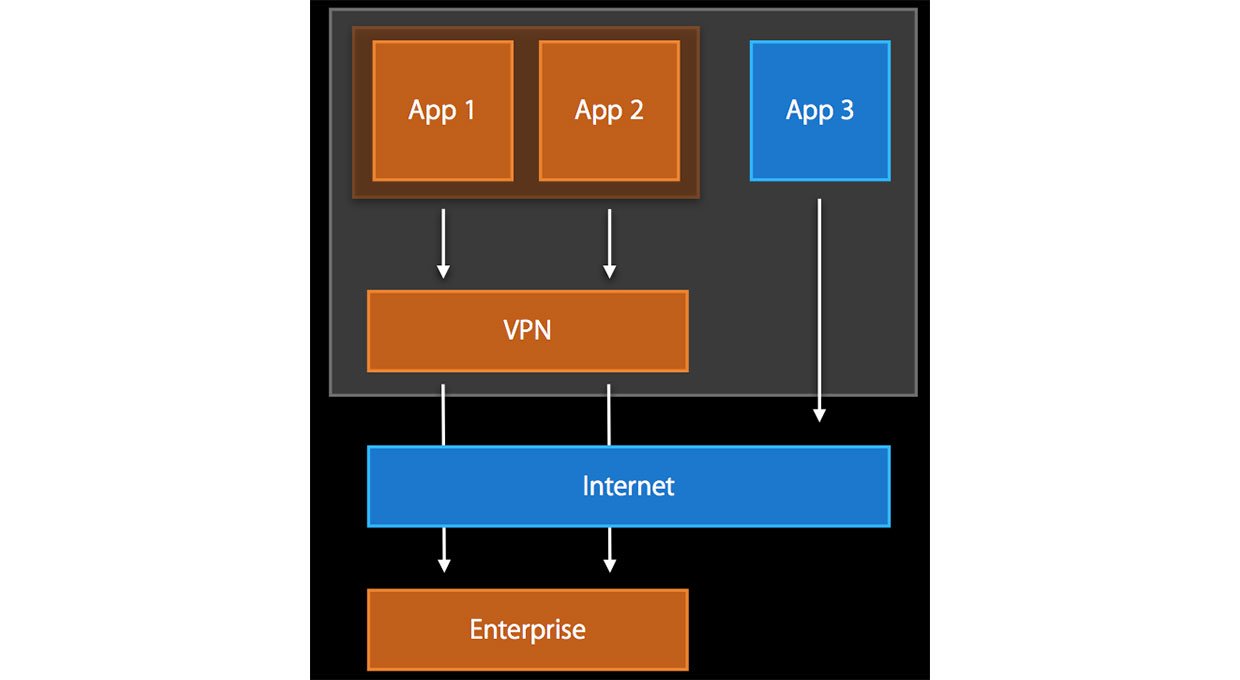
 In iOS 7, an IT administrator can specify a VPN per app. This means that only the apps that are provided by your company, and need company data, will start and use the VPN connection. Apps that are personal will simply connect to the Internet as they normally do. Apps managed and installed by your company are pre-configured at installation time to use a specific VPN connection. This approach is by far more desirable than the current iOS 6 approach.
Default Encryption Class for all Installed Apps in iOS 7
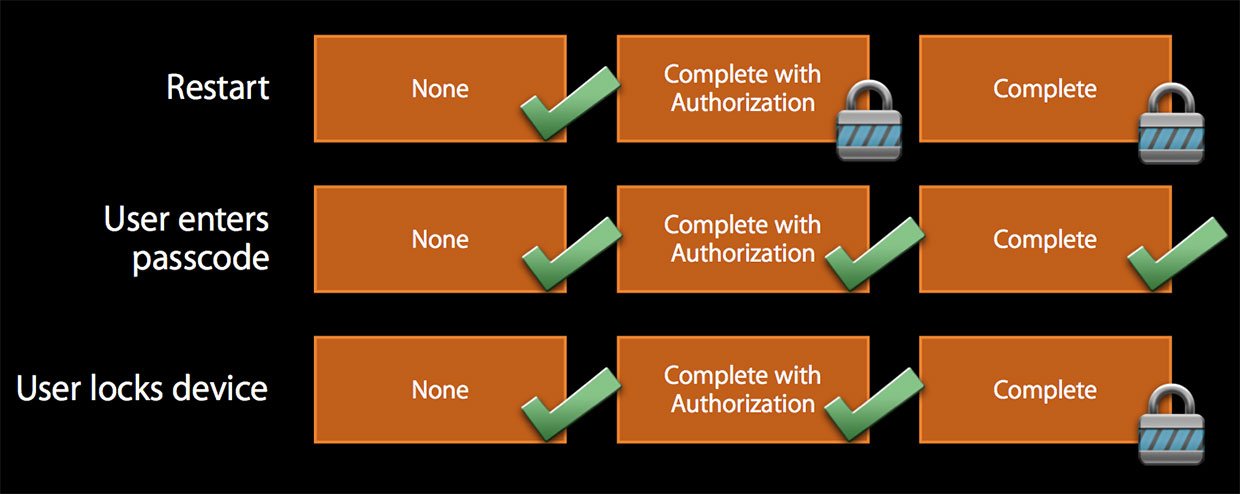
On all versions of iOS, including iOS 7, an app developer can choose to use one of three encryption classes for the files their app writes.
- None. This means that no encryption is applied to the file
- Complete With Authorization. This means that after the iOS device is rebooted, the data is encrypted until the user enters their device password the first time. After that the data remains unencrypted, even if the device is locked.
- Complete - This means that a file's data is encryption always until the user types in their device password and then it remains unencrypted until the device locks. The data is then encrypted again until the user enters the device password again. So essentially whenever the device is locked, the data is encrypted.
The encryption used by devices running iOS 6 and later have the US government's very stringent FIPS-140-2 certification which not only means that the encryption is excellent, but it means that iOS devices are able to be sold into the US government.
In iOS 7, this remains the same however any new apps that are installed will automatically be assigned to the Complete with Authorization class so that after a device reboot, the data will remain encrypted on the device until the device password is entered.
Prevent Keychain Secrets From Being Restored To A New Device in iOS 7
The encryption classes mentioned above also apply to items in the Keychain and in iOS 7 you are now able to set a new attribute which prevents Keychain secrets from being backed up from one iOS device and restored onto another one. This ensures that the Keychain secrets will only ever be revealed on one iOS device.
Manage Apple TV in iOS 7
Apple TVs are so cheap at $99 that they are ideal for classrooms and conference rooms. Using AirPlay, teachers in classrooms, or presenters in conference rooms can easily do screen mirroring from their iOS or OSX devices, or simply stream PowerPoint presentations or videos from their devices to the Apple TV. In iOS 7 (running on your Apple TV), IT administrators via the use of their MDM system, will now be able to enroll and control Apple TVs.
Using the MDM system, IT administrators will be able to do things like set the language and locale as well as pre-setting up 802.1X payloads for secure network access.
Manage AirPlay Mirroring in iOS 7
In iOS 7, an IT administrator can, via an MDM system, pre-setup iOS devices to start mirroring to a specific Apple TV, and also setup Apple TV whitelists and Apple TV passwords.
Streamlined MDM Device Enrollment for Company Provided iOS 7 Devices
Apple has added a much improved and streamlined method for enrolling company provided iOS devices (that is devices a company purchases and provides to their employees). This new enrollment method is not for Bring Your Own Device (BYOD)
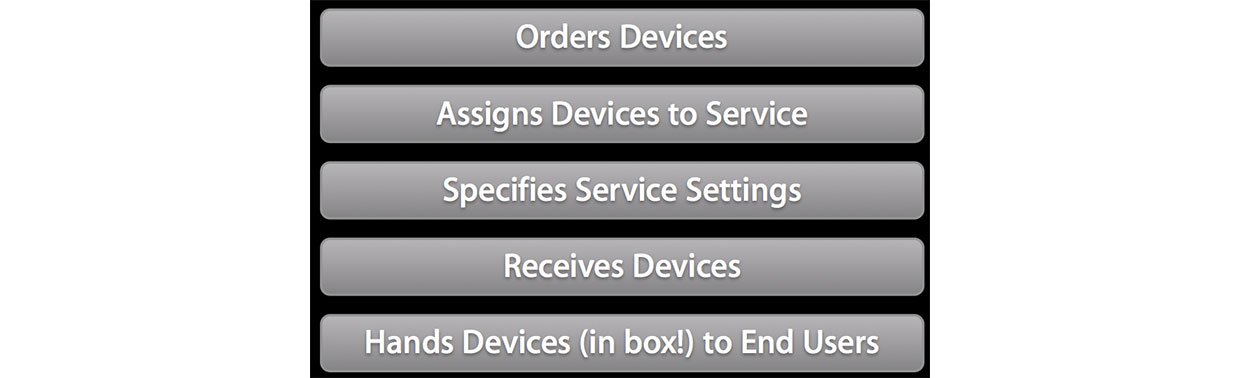
It is a two-step process.
- The company purchases devices and assigns them to the new Apple Enrollment Service, providing the enrollment settings (which include the URL for your MDM solution, and certain enrollment settings including the ability to skip device setup screens). This enrollment process can be handled via an MDM solution.
- The employee gets their new iOS device sealed in the box and since the enrollment steps are built right into the device setup screens, simply runs through the normal setup screens. Because enrollment is now built into the device setup, the user will be prompted to login to your organization.
 The architecture of this new enrollment mechanism is as follows.
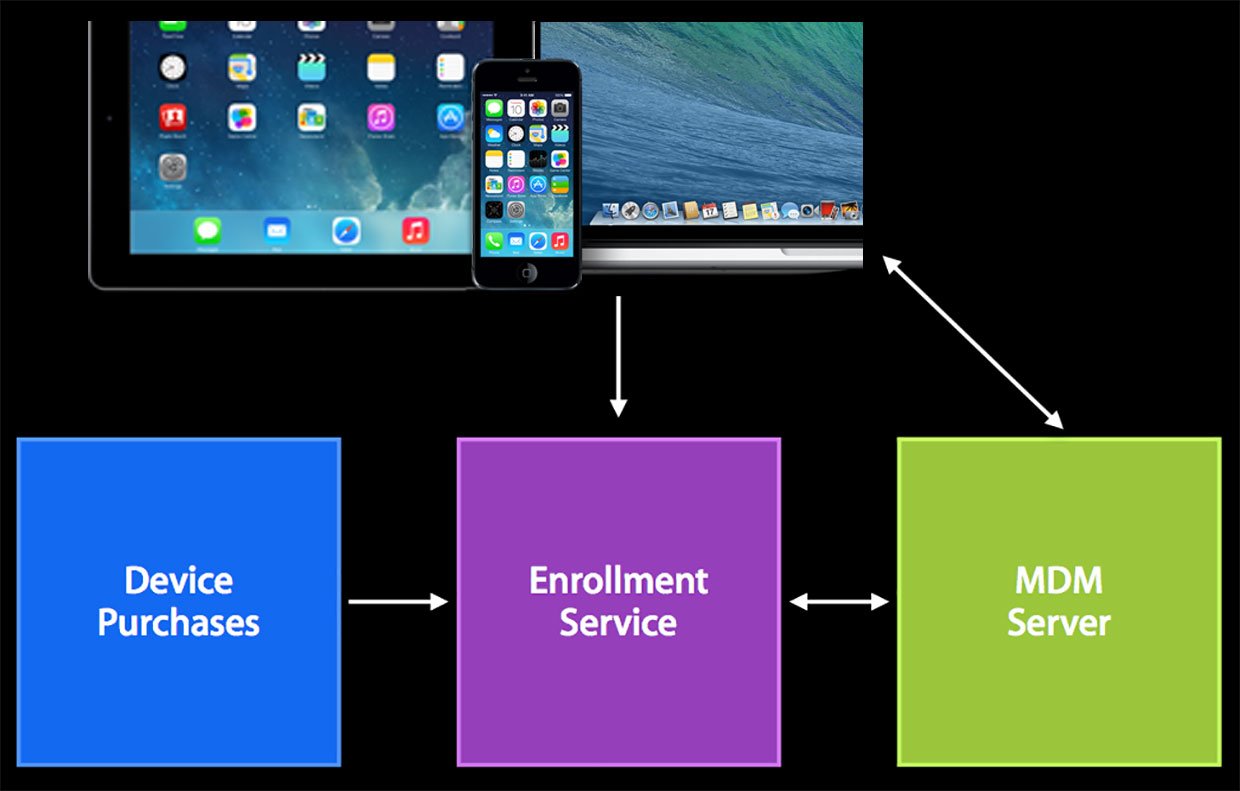
You'll notice from this architecture diagram that the MDM solution you use will be able to interact with the new Apple Enrollment service and your iOS and Mac devices to provide this automatic enrollment.
AirPrint In The Enterprise in iOS 7
AirPrint is a print protocol that allows for seamless and driverless printing from iOS and OSX devices. AirPrint printers (of which there are a lot – here's the list) are available to iOS and OSX devices via Wi-Fi and Ethernet connections, but in the future also via USB. The Bonjour protocol is used to find them but AirPrint printers can also be added to a company's Domain Name Server (DNS) as static printers and the iOS or OSX device is able to query DNS to find AirPrint printers.
AirPrint also supports IPPS (Secure IPP with TLS) for those worried about someone sniffing the contents of a print job going to an AirPrint printer.
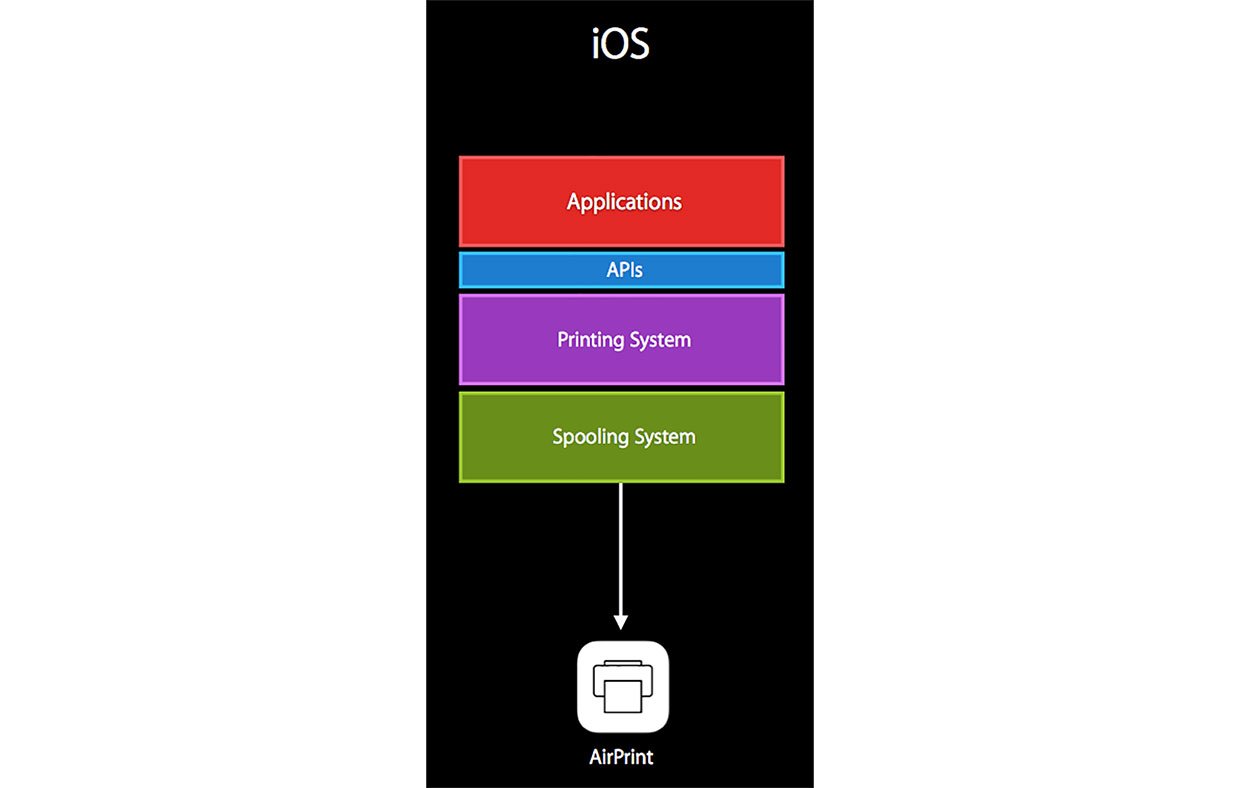
 In iOS 7, via an MDM system, an administrator can pre-define AirPrint printers to iOS devices.
AirPrint has also added a few new classes of printers of interest to the enterprise that include Roll Fed printers, enterprise class laser printers, label printers, and Dye-sub photo printers.
Later this year certain consumer and enterprise print server manufacturers will be adding support for AirPrint which means that using AirPrint, iOS and OSX users will be able to print to any printer (no matter if it support AirPrint or not) attached to one of these print servers.
One anecdote about developing apps that you want to support AirPrint in, XCode includes a printer simulator that makes seeing your app's output very easy, certainly easier and cheaper than printing to a real printer.
Multipeer Connectivity in iOS 7
Multipeer connectivity is a new feature in iOS 7 that allows many iOS 7 and higher devices to communicate with each other over Bluetooth, Infrastructure Wi-Fi, and Peer to Peer Wi-Fi. Once connected devices can send message type data or stream data between devices.
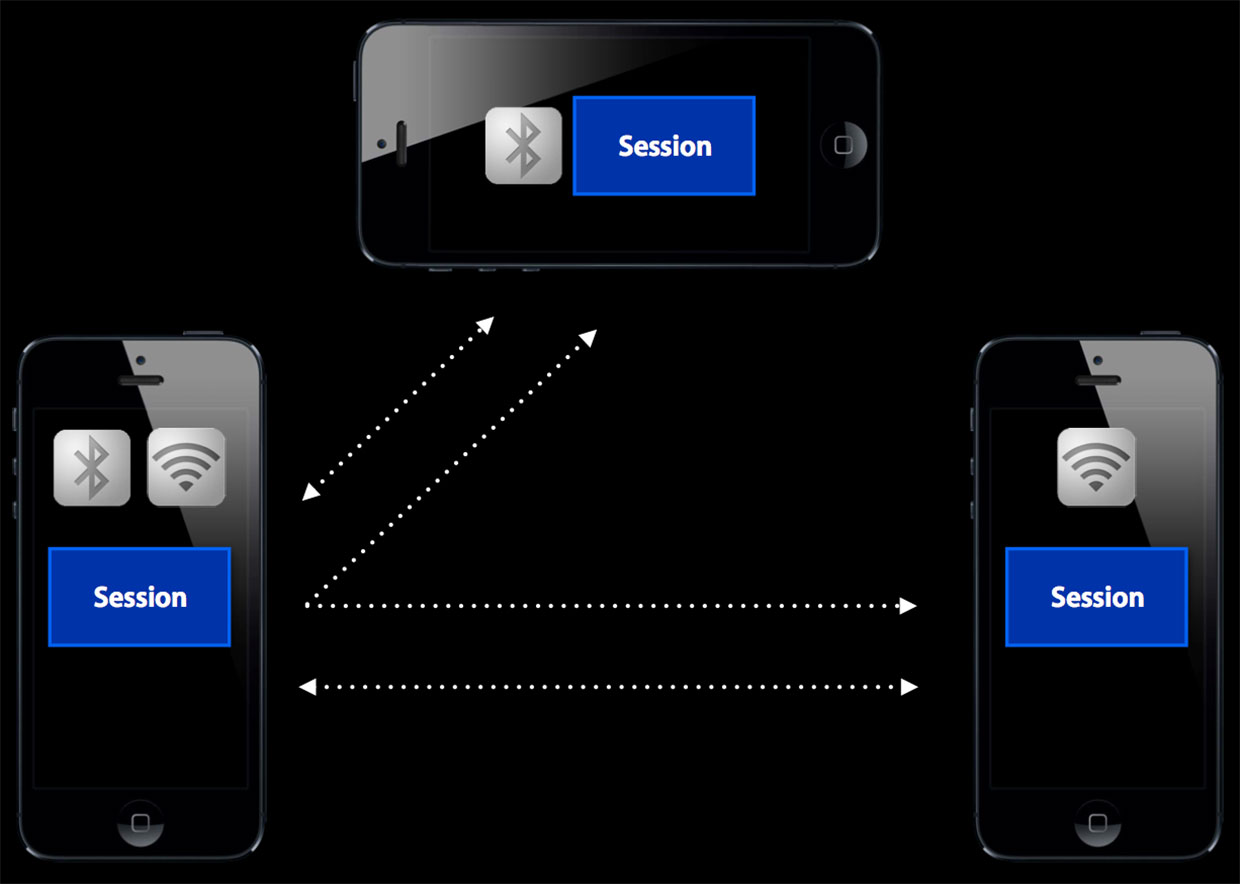
 Since the process of connecting devices has been abstracted from the developer, it makes writing apps to support this technology very easy, in fact down to the point where the framework will use multiple radios to ensure that all device can communicate with one another no matter which radios each one may have enabled.
There is much more to read about Multipeer connectivity but I wanted to point out that this technology supports authentication and data encryption. This makes is possible for enterprises to make use of it since connections can be forced to be authenticated and the data is encrypted.
Multitasking For All Apps in iOS 7
iOS has for a while now, allowed certain apps (like GPS, VoIP, and streaming audio apps) to run in the background, but all other apps go to sleep and are paused once the user switches to another app or the device goes to sleep.
In iOS 7, any app can run in the background but in a manner that is conscious of battery life. You can read more on how iOS 7 handles multitasking but in the enterprise space this allows apps to be more up to date and new content available to the user before they switch to the app.
64-bit in iOS 7 (iPhone 5S and later)
iOS 7 is now a full 64 bit mobile operating system which provides short and long-term gains. In the short term it means a performance boost for the iPhone running on the Apple A7 chipset, as long as all apps running on it are 64 bit. This is because the 64-bit CPU provides twice as many integer and floating-point registers as the previous 32-bit CPUs allowing 64-bit apps to work with more data at once for improved performance.
Core iOS apps will ship as 64-bit apps of course.
Number crunching and working with more data at once will allow companies to create better number-crunching apps like financial dashboards, but also graphics intensive apps.
Biometrics in IOS 7 (iPhone 5S and later)
Touch ID is fingerprint ID sensor on the iPhone 5s that handles biometric authentication and authorization via a reader on the Home button and a secure enclave on the Apple A7 chipset. The Touch ID system is completely secure, and returns a simple yes/no response to iOS 7, which will then unlock or authorize a transaction. One of the biggest corporate hurdle is end-point security. Ask any Risk Management officer at a company what keeps him up at night and he or she will tell you that it is weak passwords.
Sure you can make your users enter 10 character alphanumeric passwords with special characters because it provides greater security, but you will likely be overruled by other company officers who want to make it easier to enter and remember those passwords. This ultimately leads to a compromise that makes the end-points unsafe.
Using your fingerprint to unlock your iPhone in a one-step motion will make Rick Managers happy, and your iPhone more secure.
Additional MDM queries and controls
There are additional MDM features in iOS 7 that don't fit into the above categories
Prevent Account Changes
This feature allows an IT administrator to prevent an iOS user from making changes to or removing accounts on the device. This prevents a user from tampering or removing a corporate account, for example to connect to Exchange.
Host Pairing
This feature allows an administrator to control which devices an iOS 7 device can pair with. In iOS 6 and below, pairing was uncontrolled.
Remaining New MDM Restrictions and Queries
No information was provided about the restrictions and queries below so I am just listing them for completeness, however many are self-explanatory.
- Wallpaper Changes
- Find My Friends Changes
- Define Service for Text Selections
- Limit Ad Tracking
- iCloud Keychain Sync
- Over-The-Air PKI updates
- Lock screen Wi-Fi and Airplane Mode buttons
- Ability to Set a Custom Lock Screen
- Put a device in Lost Mode
- Disable Personal Hotspot
- Query a device to see if it has the HotSpot enabled
- Query the device to see if has Do Not Disturb enabled
- Query the device to see if it has Find My iPhone enabled
- Query the device to see if it has an iTunes account signed in.
The Bottom Line
Since iOS 4, Apple has been catering to the enterprise, government, and education space through the implementation of hardware file system encryption and the plethora of MDM controls that can be used to tightly control iOS devices.
iOS 7 has made the case for iOS in Enterprise, Education, and Government stronger. Even if Apple's primary audience is the consumer, it has been quietly supporting the enterprise in a big way which is the reason we see much more iOS than Android in the enterprise space.
- Complete iOS 7 review
- More iOS 7 tips and how-tos
- iOS 7 help and discussion forums
Craig Johnston is a Mobile Strategist at NTT DATA and has been designing and managing large scale enterprise networks since 1989, including massive BlackBerry, iPhone, and iPad deployments in Fortune 500 companies. An avid podcaster and writer, you can find his books on Amazon and follow him on Twitter @ibanyan.

