iOS and macOS users served up 1 Billion popups thanks to Chrome and Safari exploits
What you need to know
- More than a billion popups were able to exploit bugs in Apple's WebKit and Blink, which powers Chrome.
- A bug spotted in August was very similar to one used in April by the same group.
- eGobbler is the group behind the malicious ads.
Reports today from TNW suggests that Malvertiser eGobbler was able to exploit "obscure" bugs in WebKit and Chrome to hit iOS and macOS users with over 1 billion malicious popups in less than two months.
According to TNW:
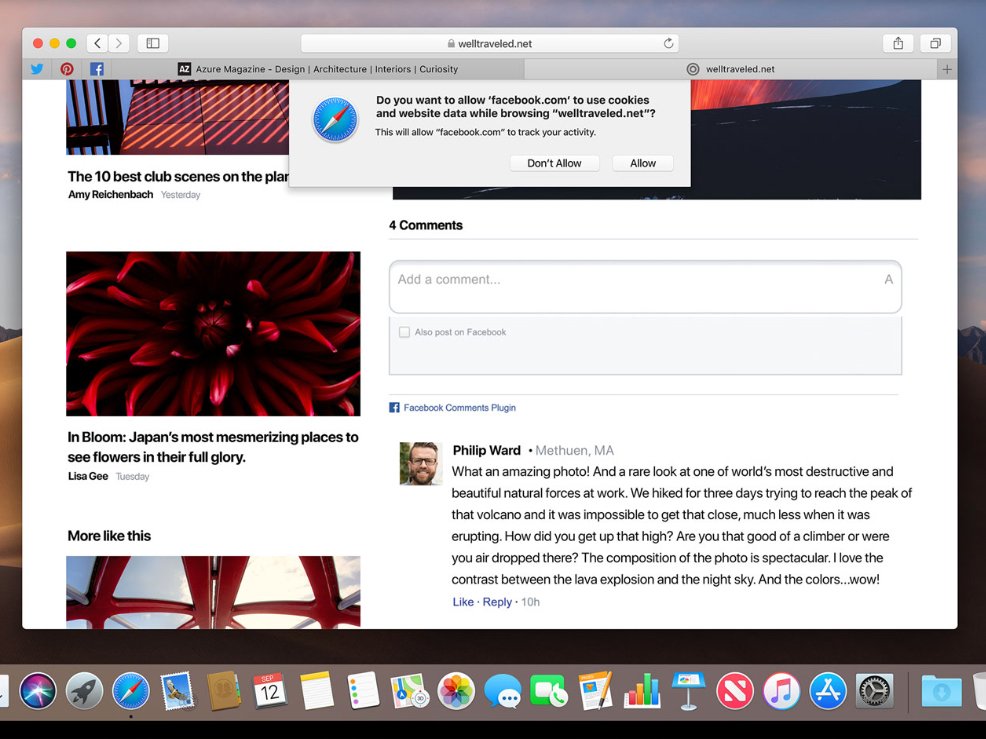
The attackers targeted iOS and macOS users with zero-day vulnerabilities in Chrome and Safari browsers that bypassed built-in security protections to show potential victims intrusive pop-up ads, and redirect users to malicious sites.
The research revealing this was carried out by Cybersecurity firm Confiant, who has been tracking eGobbler. Confiant raised awareness of an exploit in Chrome back in April of this year. Google fixed this in Chrome 75 on June 4. However, at the beginning of August Confiant claims that another eGobbler payload similar to the first was discovered. They note:
While this payload looks similar to the prior Chrome exploit on the surface, we found it peculiar that eGobbler would still be running outdated exploit code that was fixed months ago, so we recreated our test environment and staged the payload across over two dozen devices and browser versions. This time around however, the iOS Chrome pop-up was not spawning as before, but we were in fact experiencing redirections on WebKit browsers upon the 'onkeydown' event.
This new bug was reported to Chrome and to Apple, the Chrome team submitted a patch to WebKit on August 9, and Apple released a fix on September 19 in iOS 13, and September 24 in Safari 13.0.1 Despite Confiant raising the alarm quickly, they estimate that between August 1 and September 23, 1.16 billion malicious ads were viewed as a result of the flaw.
The news is proof that security is one of the most important reasons as to why you should try to keep all your software as up to date as possible.
iMore offers spot-on advice and guidance from our team of experts, with decades of Apple device experience to lean on. Learn more with iMore!

Stephen Warwick has written about Apple for five years at iMore and previously elsewhere. He covers all of iMore's latest breaking news regarding all of Apple's products and services, both hardware and software. Stephen has interviewed industry experts in a range of fields including finance, litigation, security, and more. He also specializes in curating and reviewing audio hardware and has experience beyond journalism in sound engineering, production, and design.
Before becoming a writer Stephen studied Ancient History at University and also worked at Apple for more than two years. Stephen is also a host on the iMore show, a weekly podcast recorded live that discusses the latest in breaking Apple news, as well as featuring fun trivia about all things Apple. Follow him on Twitter @stephenwarwick9

