Checkm8, the iPhone 4s to iPhone X bootrom exploit, explained

Checkm8 is a bootrom-level security exploit that can be used against every iPhone from the 4S to the X. It was announced late last week by axi0mX — axi0mX… axi0m10… dammit, Apple! — and ever since we've seen everything from fear, uncertainty, and doubt, to supremely good reporting on what it is, what it isn't, and most importantly, what it means for all of us.
So, let's try to sort it all out.
Now, before we dive in, I'm not an infosec expert nor do I play one on the internet. Checkm8 is absolutely serious but very specific and in some ways very limited. It's certainly helpful for jailbreakers and researchers that it exists, probably neutral good for bad actors, and bad for Apple and a black eye for iOS security that'll no doubt drive them even harder to lock things down even better, again.
But, for the average user, the threat level today probably isn't any different than it was a week ago. I'm going to sum up why as best and as accurately as I can, but I'm also going to link up some terrific work by Ars Technica and Malwarebytes in the description. Hit them up for much, much more. Cool? Cool.
So, what's a bootrom exploit?
Bootrom, or secureBoot, is the very first code that runs on an iOS device when it starts up. It lives on a ROM, or read-only memory chip, at the very lowest level of the device, and it typically can't be changed.
A bootrom exploit, then, is an exploit that targets a bug in the Bootrom. That's as opposed to the far, far more common exploits that target bugs at the higher operating system level.
While operating system exploits are far more common, they're also far more easily fixed. Pretty much every time Apple updates iOS, the new version patches security issues with the old version.
iMore offers spot-on advice and guidance from our team of experts, with decades of Apple device experience to lean on. Learn more with iMore!
Not so with bootrom exploits. Because they're in ROM, they're nigh-impossible to patch. I mean, never say never, but so far, every device with a bootrom that's exploited stays exploited.
And checkmate exploits every device with an A5 to A11 chipset.
Um… which devices are those exactly?

So far, devices affected by checkm8 include:
- iPhone 4s to iPhone X.
- iPad 2 to 7.
- iPad mini 1 to iPad mini 4.
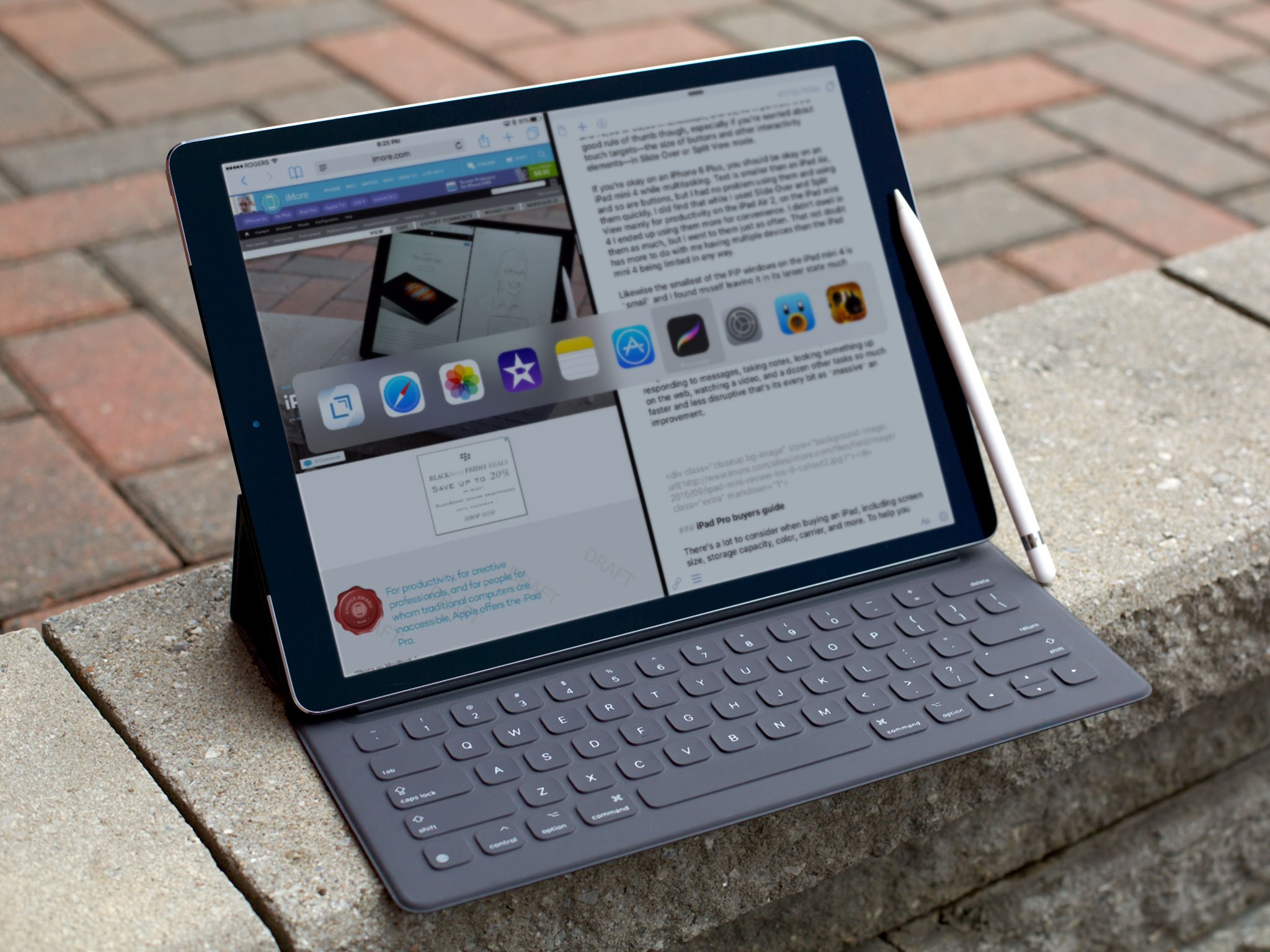
- iPad Pro 1 and 2.
- Apple TV 3 to 4K.
- iPod touch 5 to 7.
Earlier iPhones, iPads, iPods touch, and the like aren't affected by checkm8 (though there are earlier bootrom exploits.). The new entry-level 10.2-inch iPad and iPod touch 7 are on A10, so they're the only current devices currently affected.
Checkm8 doesn't work on A12 or A13, so that means the following devices are NOT affected:
- iPhone XR, XS, 11
- iPad Air 3
- iPad mini 5
- iPad Pro 3 (2019)
As to why, the developer told Arn Technica:
There were changes to make [newer chipsets] not exploitable. All I know is I can't get it to work. For me, it's not something that I can do. What I do involves using multiple bugs. Some that are not serious might be required to access other bugs that are more serious. Because Apple patched some bugs in the newer phones, it can no longer be exploited as far as I know.
Wait, is checkm8 a jailbreak, and attack, something else?
Checkm8 is an exploit, and that's it, at least for now.
It's something that could and probably will turn into a jailbreak sooner rather than later, but also has some very limited, very targeted potential to be turned into an attack as well.
Given what it is and those limits, though, it's probably not something most of us have to worry about.
Why would an attack be limited?

There are a few things that limit Checkm8's potential as an attack.
First, it can't be executed remotely. Someone has to take physical possession of your iPhone, iPad, or other iOS device first, but it in DFU or device firmware update mode, and then plug it into a PC over USB before they can even use the exploit.
Second, Apple has a secure boot chain, so every step is checked by the previous step. And if the signatures aren't verified, the software won't run.
Checkm8 can't rewrite the bootrom, it can only exploit it. Here's what that means, according to what the developer told Ars:
I can't write my code into the read-only memory, so my only option is to write it into RAM or, in this case, SRAM—which is the low-level memory that is used by the bootrom—and then have my injected code live in this small space. But the actual bootrom code itself does not get copied in there. It's only the things that I added to my exploit.
But what that means is, checkm8 isn't persistent. It can be used to run unsigned code on your device, but that code only lasts until the device is rebooted. Then it goes right back to normal, and you'd have to go through the whole exploit process again to run the unsigned code again.
Third, Checkm8 doesn't compromise the Secure Enclave on the A7 or later, which means it can't beat the hardware encryption, get around Touch ID or Passcode — and doesn't work on devices with Face ID — or otherwise give anyone else access to your data or secrets.
To get at those, you would have too leave your device lying around somewhere vulnerable for an extended amount of time, an attacker would have to get ahold of it, run the exploit, get a hold of and load up malware that could try and capture your credentials, put your device back, and then try to capture them.
And, if they're a disgruntled family member with that kind of access to you and your devices, it'd be far easier to just put your finger on the Touch ID sensor or shoulder surf your passcode over time anyway.
For non-family members, again, the creator talking to Ars:
Yes, but [installing a potential back door is] not really a scenario that I would worry much about, because attackers at that level… would be more likely to get you to go to a bad webpage or connect to a bad Wi-Fi hotspot in a remote exploit scenario. Attackers don't like to be close. They want to be in the distance and hidden.
So, again, never say never.
At large scale, I'm not sure checkm8 changes the economics of iOS attacks. But, if you're concerned, and still running an A5 or A6 device, which Apple is no longer supporting or updating anyway, then add this to the voluminous list of reasons you should consider upgrading asap.
And, if you think, based on who you are or what you do, that you have a much higher potential threat level, then you've probably already, routinely upgraded to the latest silicon anyway.
But, jailbreak, exciting, right?

Jailbreakers are probably the most excited about Checkm8. Now, nowhere nearly as many people jailbreak as they used to because iOS has continued to add more and more of the functionality that people used to jailbreak for. But, the ones that do, the customizers, the tweakers, the unsigned appers — they're every bit as passionate as ever.
And this is like the second coming of the holy grail for them, basically because it's been so long since they've had a jailbreak built off of a bootrom level exploit.
What makes it so attractive to jailbreakers is that, unlike operating system exploits, which have led to jailbreaks as recently as iOS 12 this year, bootrom exploits don't get blown away the very next time Apple releases a software update.
So, the jailbreakers can relax and enjoy their open systems, and likely with any version of iOS past, present, and future, for as long as they're using one of the affected devices.
With a few caveats.
First, it'll only be those devices, iPhone 4s to iPhone X, primarily, and as time passes those devices will be less and less modern and interesting.
Second, even when the jailbreak comes, it will be a tethered jailbreak. At least for now.
That means, yes, putting the device in DFU or device firmware update mode, connecting the device to a PC with a USB cable, and running the jailbreak every time it reboots.
And that might be just enough of a hassle that it'll relegate long term use to the hardcore rather than just the curious.
And researchers?
Security researchers are likely the group that benefits the most from checkm8, at least in the short term.
Up until a month or so ago, when Apple announced their new bug bounty program and research-fused devices, researchers had to come up with their own exploit chains or get their hands on blackmarket dev-fused devices to even get into iOS and start poke around.
So, having a likely irrevocable bootrom level exploits, even if only for older devices, will make researchers lives just that much easier. Basically, it solidifies the first link in the exploit chain for them, and they can just get on with everything else.
And even before Apple starts shipping those research-fused devices.
What about nation states?
What does this mean for nation states and government agencies, and the companies that supply exploits and devices to them?
Much the same.
Politics bends everything, including the economics of iOS attacks. But, these entities typically have exploits of their own already. At most, checkm8 will supply them with an alternative to what they already have, and one that can't be blown away by an iOS software update in the future. Though, again, only on older devices.
They'll still need their own exploits for more recent devices, and because checkm8 doesn't get around the secure element or passcode or Touch ID, they'd still need their own exploits for the rest of the chain as well.
The developer, speaking with Ars:
I don't think that they can do anything today with Checkm8 that they couldn't do yesterday [without Checkm8]. It's just that yesterday maybe they would do it a slightly different way. I don't think they gain anything from this release.
So, again, if based on your work or just who you are, you think you're potentially at higher risk from Checkm8 specifically, you can protect yourself by making sure you're on an A12 or A13 device.
So, do I need to worry about checkm8?
Checkm8 is an incredible piece of work. You only have to look at how long it's been since the iOS bootrom was last exploited to understand just how much axi0mX has really accomplished.
But, for right now, this is also so very inside baseball, and not something the average fan in the field is even going to see.
So, stay informed, absolutely. Follow those links in the description if you want to learn more about int, please.
But don't lose any sleep over it, or let anyone steal any of your time with attention bait.
One part of an iOS exploit chain has been made stable for a series of older devices.
Apple has to address that, and address how they're handling iOS security in general in an age where so many eyes and minds are on them.
It's already fixed in newer devices, but Apple has to figure out new and better ways to keep it from happening with current and future devices. It's been a decade since it's happened before but the goal should, and I'm kinda guessing is, forever until it happens again.
But that's all on Apple. For us, again again, anyone at all concerned by checkm8, if you haven't already, upgrade to an iPhone XR, XS, or 11, or a current or eventually later-generation iPad Pro.
And then checkm8 will be checked out of luck.

Rene Ritchie is one of the most respected Apple analysts in the business, reaching a combined audience of over 40 million readers a month. His YouTube channel, Vector, has over 90 thousand subscribers and 14 million views and his podcasts, including Debug, have been downloaded over 20 million times. He also regularly co-hosts MacBreak Weekly for the TWiT network and co-hosted CES Live! and Talk Mobile. Based in Montreal, Rene is a former director of product marketing, web developer, and graphic designer. He's authored several books and appeared on numerous television and radio segments to discuss Apple and the technology industry. When not working, he likes to cook, grapple, and spend time with his friends and family.
