How to set your Mac's firmware password (and why you shouldn't)

Want to keep your roommate from posting your nude selfies on Facebook? Concerned that your Mac might fall into the wrong hands? You've already got a secure password on your Mac, maybe even file encryption. What happens if someone boots off an external hard drive?
Setting a firmware password is the solution. It comes with a few consequences and drawbacks, however. Follow along to read about the risks associated with firmware passwords as well as a guide on how to set one for those that think it's still worth it.
Setting a firmware password keeps your Mac from working with another bootable volume without inputting a password. Unlike other Mac passwords that can be reset or deleted, the firmware password remains in an area of persistent memory on the Mac's motherboard.
Here are the step by step instructions for how to do it. Read on for an important note on why it may not be a good idea, however.
To set your firmware password:
- Make sure your Mac is powered off then turn it on.
- Activate Recovery Mode by immediately holding down the Command and R keys.
- Wait until the OS X Utilities screen appears.
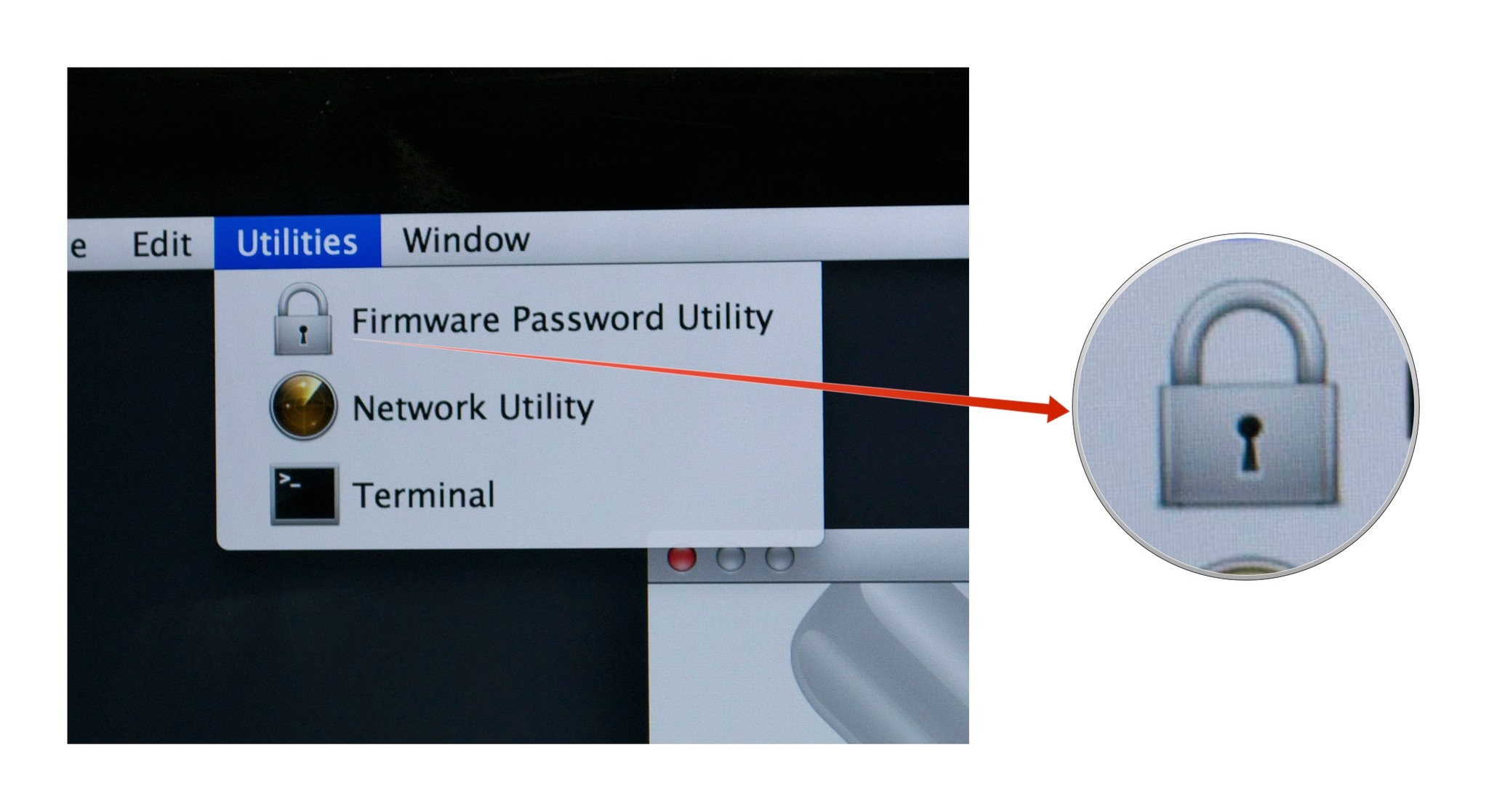
- Click on the Utilities menu from the menu bar.
- Select Firmware Password Utility.
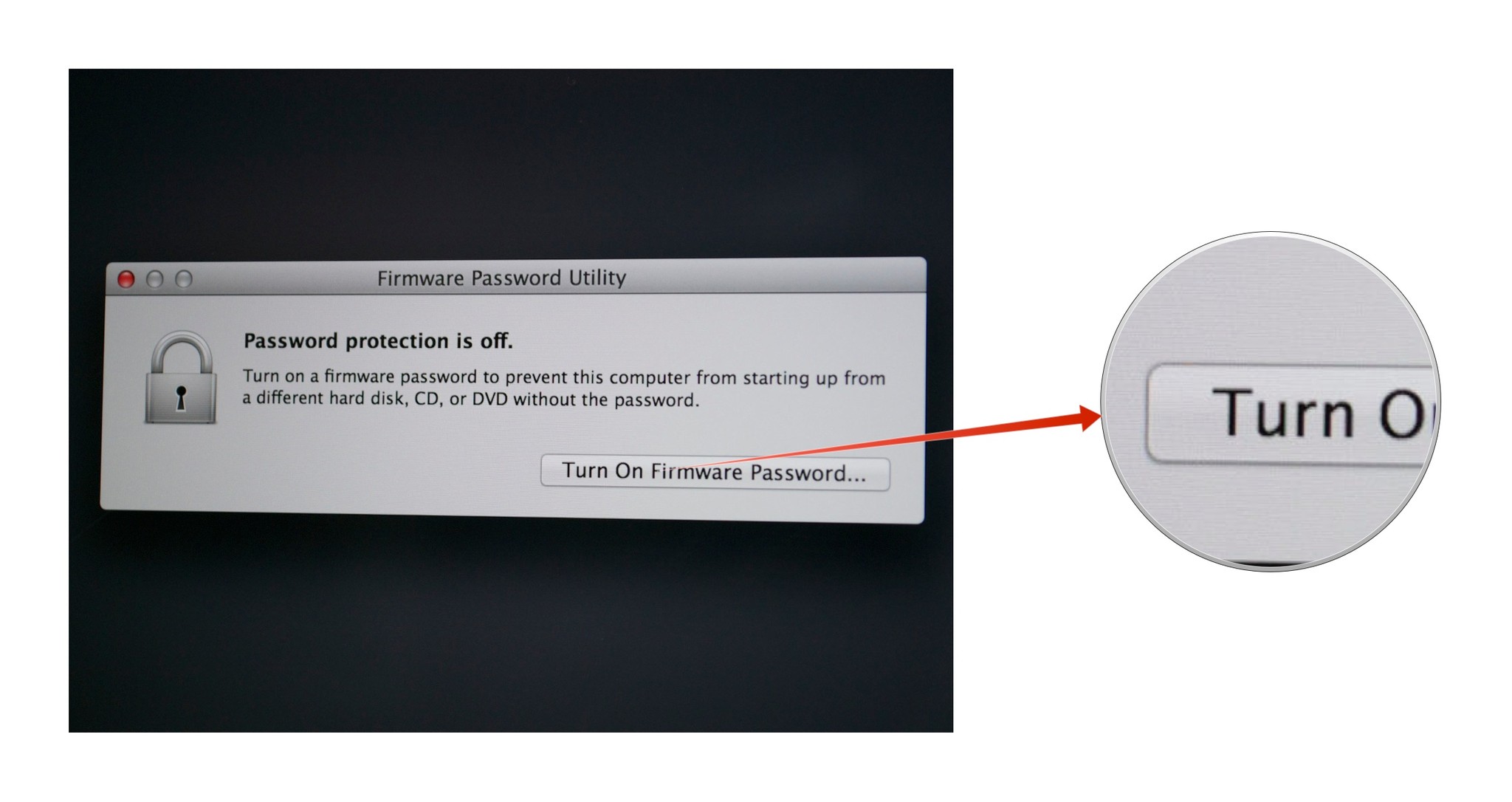
- Click on the Turn On Firmware Password...
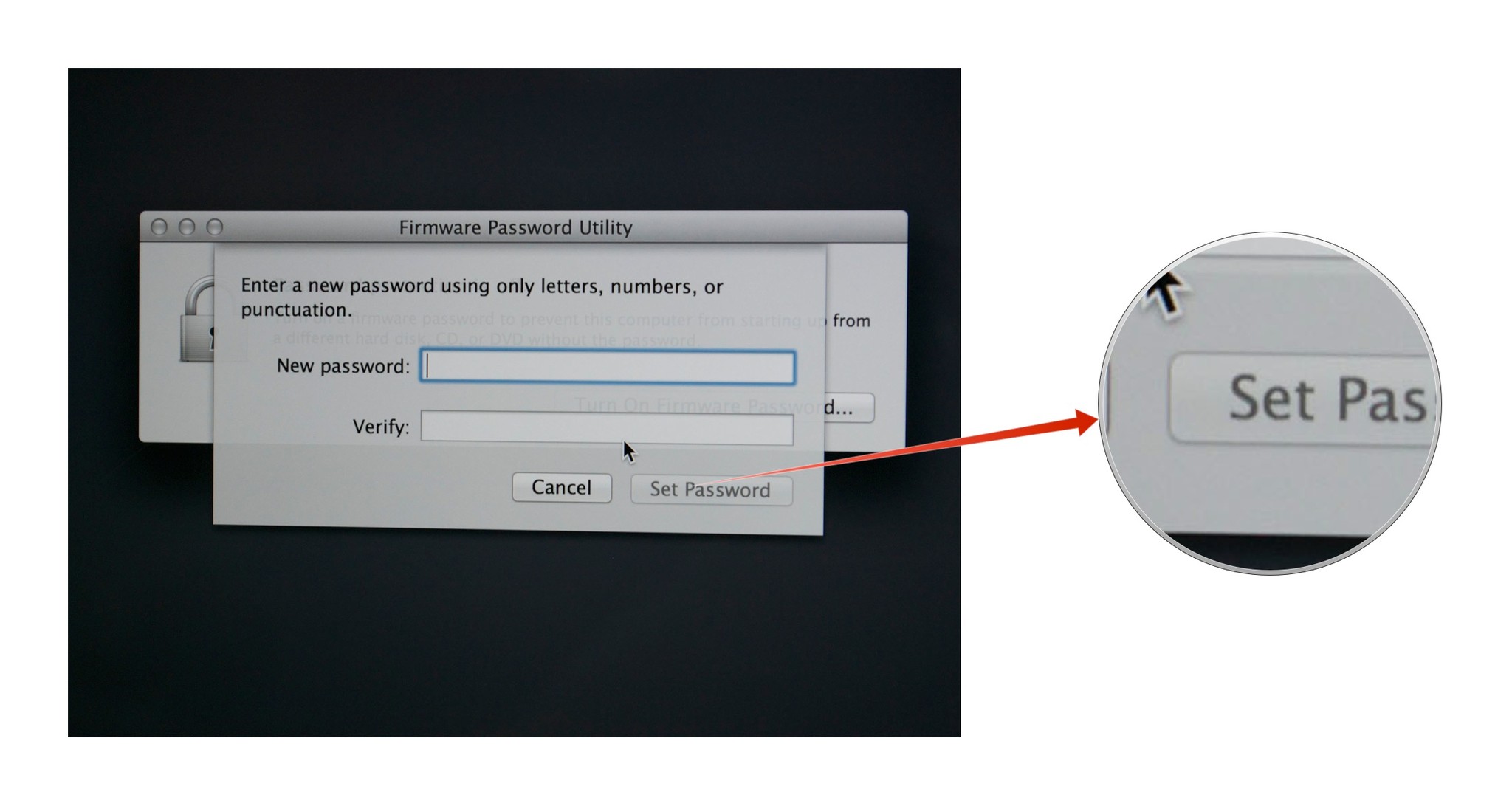
- Enter a new password, verify it and click the Set Password button.
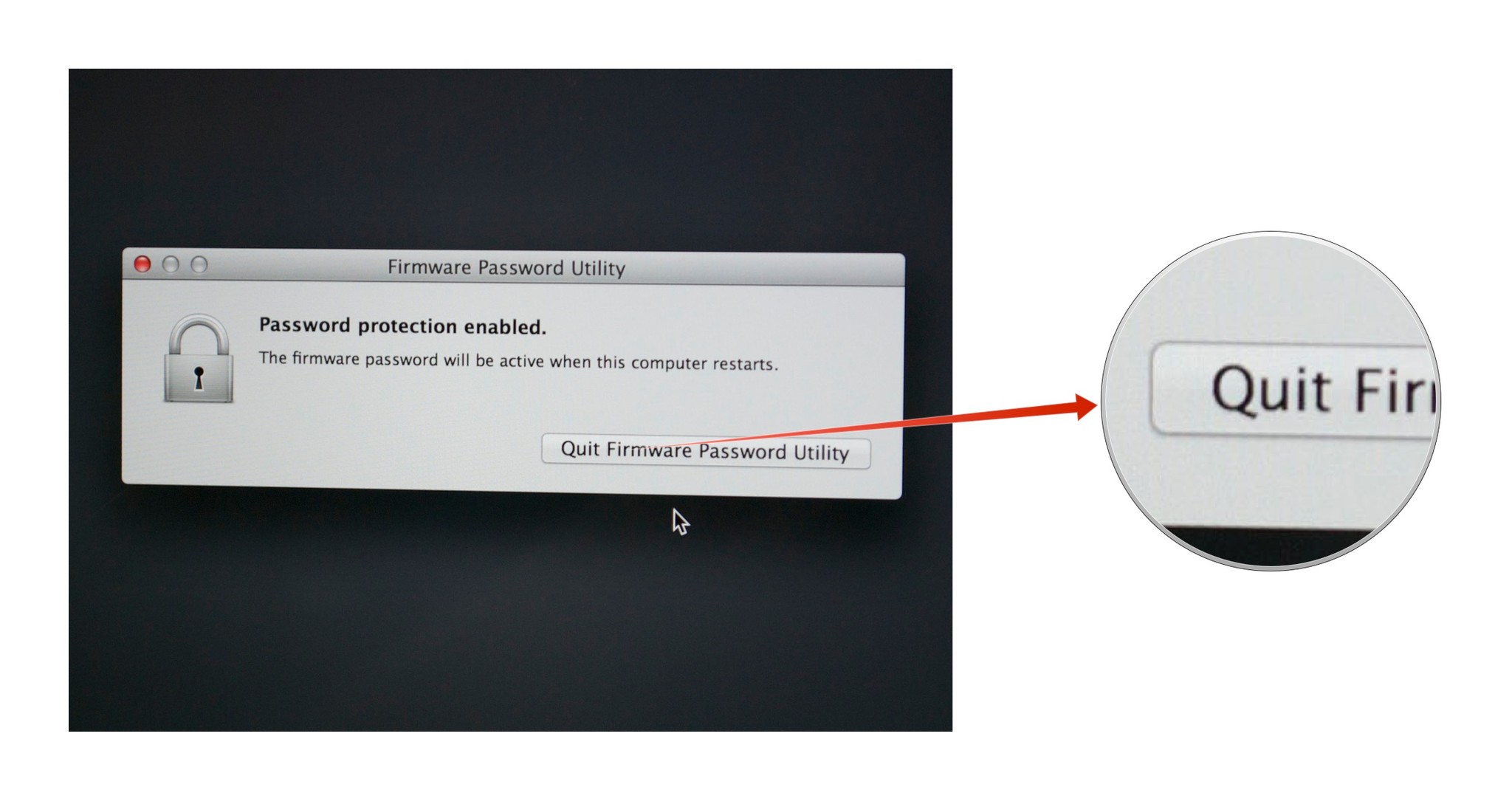
- Click on Quit Firmware Password Utility
- Click on the the menu.
- Select Restart.
Under ordinary circumstances, you won't see the firmware password field appear. The firmware password field is only visible if your Mac is booted by some alternative means, like from an external hard drive, a CD or a DVD, or if you boot the Mac in Recovery Mode or Single User Mode.
Years ago firmware passwords could be easily subverted by simply removing memory (forcing the computer's Extensible Firmware Interface, or EFI, to reset itself). Most new Mac laptops have RAM soldered to the motherboard - but even for those that have removable RAM, that loophole is closed. Apple fixed it starting with 2010 Mac models.
iMore offers spot-on advice and guidance from our team of experts, with decades of Apple device experience to lean on. Learn more with iMore!
These days your Mac's firmware password isn't easily reset. If you forget it, you're in for a long haul. In fact, Apple only recognizes one official way to reset a firmware password: Bring your Mac in to an authorized Apple Service Provider or an Apple retail store and have them do it there.
So think twice before you use this. But if you do, rest assured that you've employed some of the safest protection you can on your Mac.

