How to protect your private photos and personal data from being hacked
You don't have to be a celebrity to have your private photos and personal data hacked. Although the blame and fault of these hacks rest entirely on the criminals, each new case is a cold reminder that security in the digital world is just as urgent as that in the real world.
Whether you're storing data on Apple's iCloud, Google Accounts, Microsoft, Dropbox, or any other service, there are steps you can take to protect yourself from would-be hackers better. Here's how:
Don't use weak passwords
Everyone should know by now to avoid passwords like "password," "123456," your birthdate (or anyone's birthday), nickname, pet's name, child's name (or anyone's name). You also want to avoid any word or set of words in the dictionary and even common variations thereof, like d!ct!0n@ry.
Anything easy for you to remember is also easy for someone else to guess or "brute force."
Do use strong, pseudo-random passwords
The best passwords are blobs of pseudo-random letters, numbers, and symbols. The longer the series, the stronger the password. Most of us don't have to worry about nation-states or hackers with similar resources trying to get into our accounts. However, once you start using a password manager (see below), you might as well be as secure as possible.
Don't use the same password for more than one website
Let's say you set up your iCloud account with a strong password but use the same password to set up your account with home supply store. Then that home supply store gets hacked and, it turns out, they didn't bother to secure passwords properly. The hackers then start trying those passwords on other sites, including your iCloud account.
If your passwords are all different, one hack doesn't compromise all your accounts.
iMore offers spot-on advice and guidance from our team of experts, with decades of Apple device experience to lean on. Learn more with iMore!
Do use a password manager to store and auto-fill unique passwords
It's impossible to remember even one long, secure password, let alone dozens of unique ones for every site you visit online. That's where a password manager like 1Password or Lastpass comes in. They'll generate the long, strong passwords for you, store them, and when you go to those sites, they'll automatically fill in the passwords for you.
They also support Touch ID and copy/paste, so they're easy to use.
Don't use researchable security questions
Security questions are bad for security, and I wish companies would stop using them. If you're a public figure, Wikipedia can usually provide anyone with the answers to several common security questions. Even if you're not a public figure, Google can sometimes offer the same information. And if people get those answers, they can reset your password and try to get into your account.
So, avoid using security questions, regardless.
Do treat security questions like extra passwords
If a service insists on requiring security questions for password recovery or reset, don't use anything anyone else can research. Instead, treat security questions as extra password fields.
Generate long, strong blobs of pseudo-random characters and store them in your password manager. Then, if you ever need them, copy/paste them in.
Don't just use passwords
A password is a single factor. If that's all you use and someone somehow gets your password or security questions, they can get access to your account.
Add in a second factor, though, and the password only gets them halfway.
Do use 2-factor authentication
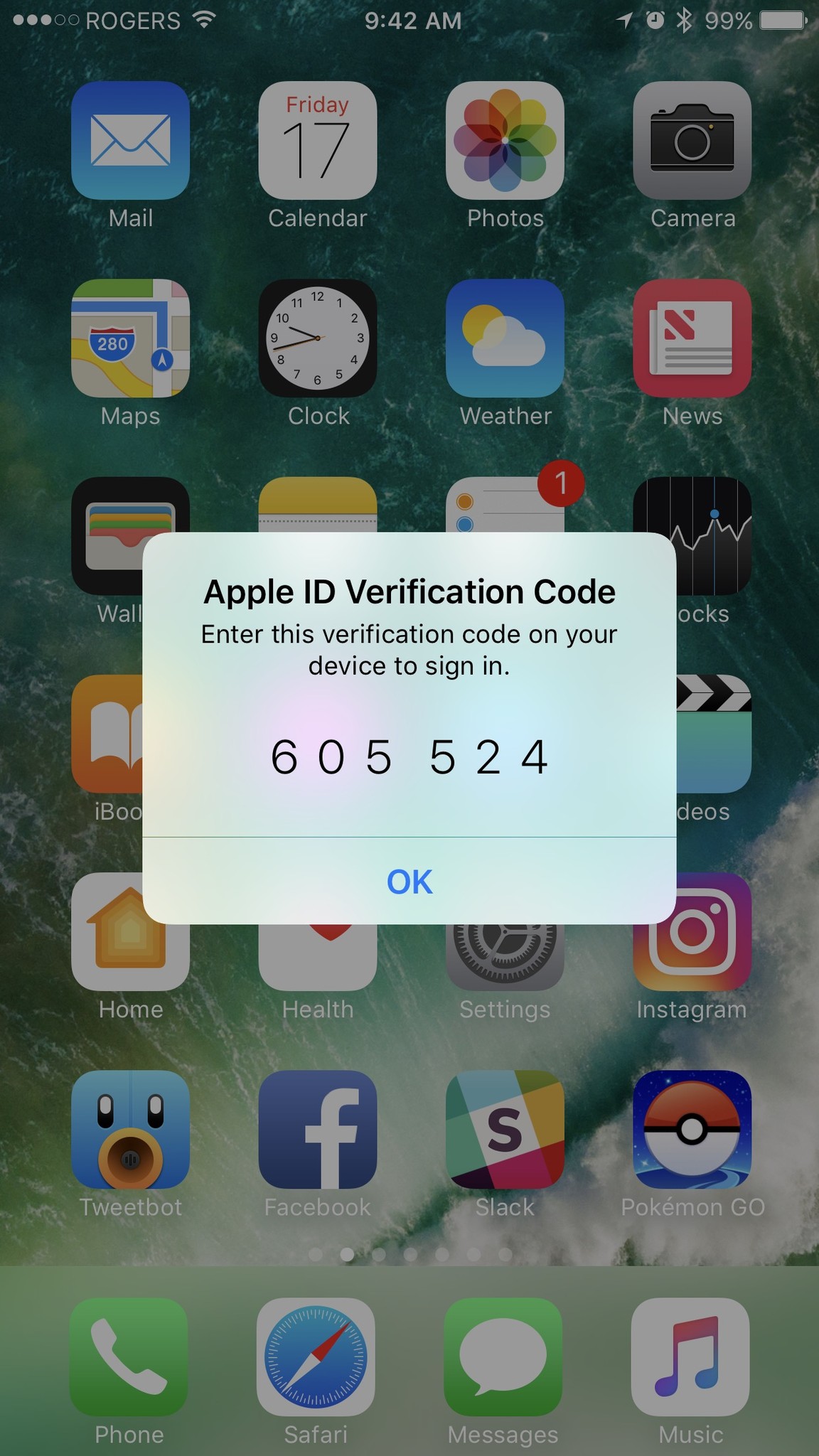
Most major online services, including iCloud, offer 2-factor authentication (2fa). Apple's version pops up a token code on your iPhone, iPad, or Mac, and you have to punch it in to get access. Other systems use apps like Google Authenticator, 1Password, or Authy to supply you with a token. (If the service only offers tokens over SMS, it's not as secure — contact them and ask them to provide proper 2-factor support.)
It's less convenient, but it's far more secure. And if the 2-factor token pops up when you're not trying to log in, you know someone else is trying to get into your account.
- How to set up two-factor authentication for iCloud
- How to set up two-factor authentication for Google
- How to set up two-factor authentication for Dropbox
- How to set up two-factor authentication for Facebook
- How to set up two-factor authentication for Twitter
- How to set up two-factor authentication for Tumblr
- How to make two-factor authentication easy with Authy
Don't click on links in emails
Phishing is when a hacker sends out volumes of fake emails saying there's a problem with your account, a special deal you can get, or anything else designed to entice you to click on a link. Spear phishing is similar, but targeted just at you and is often more personal and even more enticing.
The link is to a fake account page where they hope you'll type in your real password so they can get it. Never click a link in any email asking you to enter your login information anywhere.
How to identify and report Phishing
Do go to account sites directly
If you get an email from Apple, Google, Microsoft, Dropbox, or anyone stating there's a problem with your account, open your browser and type in the website address yourself — iCloud.com, Gmail.com, dropbox.com, etc. — and then use your password manager to log in.
If there is a problem, there should be a notification for that problem on the account page along with any real steps you need to follow.
Secure your home
Now that you've learned how to protect your personal information online, consider some of our favorite smart home security cameras:

Arlo Ultra 4K Wire Free Security Camera ($400 from Amazon)
The Arlo Ultra 4K is a security camera designed to provide ultra high resolution imagery during the day and night through 4K video and HDR support. An included LED spotlight shines when motion is detected ensuring that your recordings capture every detail, even when it is dark.

Wyze Cam Indoor Wireless Camera ($26 from Amazon)
The Wyze Cam Indoor Wireless Camera is a low-cost device that provides many of the same features that its higher-priced competitors offer. Even with its low cost, there are no additional subscriptions or fees involved, which means that the price that you pay is the only price involved.

Blink Indoor Home Security Camera ($80 from Amazon)
Blink's Security Camera is a truly wireless solution that runs on two AA batteries for up to two years. Free cloud storage makes this an economical choice for those looking for just the basics.
Any questions?
Having your data leaked is a horrible violation and should never happen to anyone. If you're storing sensitive information or content online, though, do everything you can to protect it.
Any questions or additional tips, drop them in the comments below!
Updated July 2019: We've reviewed the guidelines below and they're still the best practices to avoid having your personal photos and data leaked out onto the internet.

○ How to use two-factor authentication
○ How to protect your data from being hacked
○ How to quickly temporarily disable Face ID
○ Best practices for staying safe on social media
○ Best VPN services
○ How to lock down your data on iPhone and iPad
○ Best ways to increase iPhone and iPad security
○ How to back up your iPhone, iPad, and Mac
○ Differential privacy — Everything you need to know!

Rene Ritchie is one of the most respected Apple analysts in the business, reaching a combined audience of over 40 million readers a month. His YouTube channel, Vector, has over 90 thousand subscribers and 14 million views and his podcasts, including Debug, have been downloaded over 20 million times. He also regularly co-hosts MacBreak Weekly for the TWiT network and co-hosted CES Live! and Talk Mobile. Based in Montreal, Rene is a former director of product marketing, web developer, and graphic designer. He's authored several books and appeared on numerous television and radio segments to discuss Apple and the technology industry. When not working, he likes to cook, grapple, and spend time with his friends and family.
