Face ID hasn't been hacked: What you need to know

Face ID, Apple's facial identity sensor for iPhone X, is new and that's both scary and ripe for exploitation. We saw it happen with Touch ID, from all the concern that manifested when Apple announced it alongside iPhone 5s to the sensationalized headlines and the attempts to spoof it after it launched. Now, we're seeing the same thing with Face ID — fear, uncertainty, and doubt spread before it was even released and spoof attempts are following in a post-video-first, think-through-the-logic-flow second frenzy.
It's a shame. Face ID is incredibly enabling and accessible technology that can all but eliminate active authentication for users and allow them to unlock and use their iPhones more simply and easily than ever before. But those same people, the ones who could benefit the most, are being assaulted by an endless stream of headlines that are, bluntly, worse attacks than many of the so-called exploits they claim to be reporting.
I know this because every time one of those headlines goes live, I get calls and messages from my family members who are suddenly panicked by them. And they don't deserve that. Nobody does.
Face ID facts
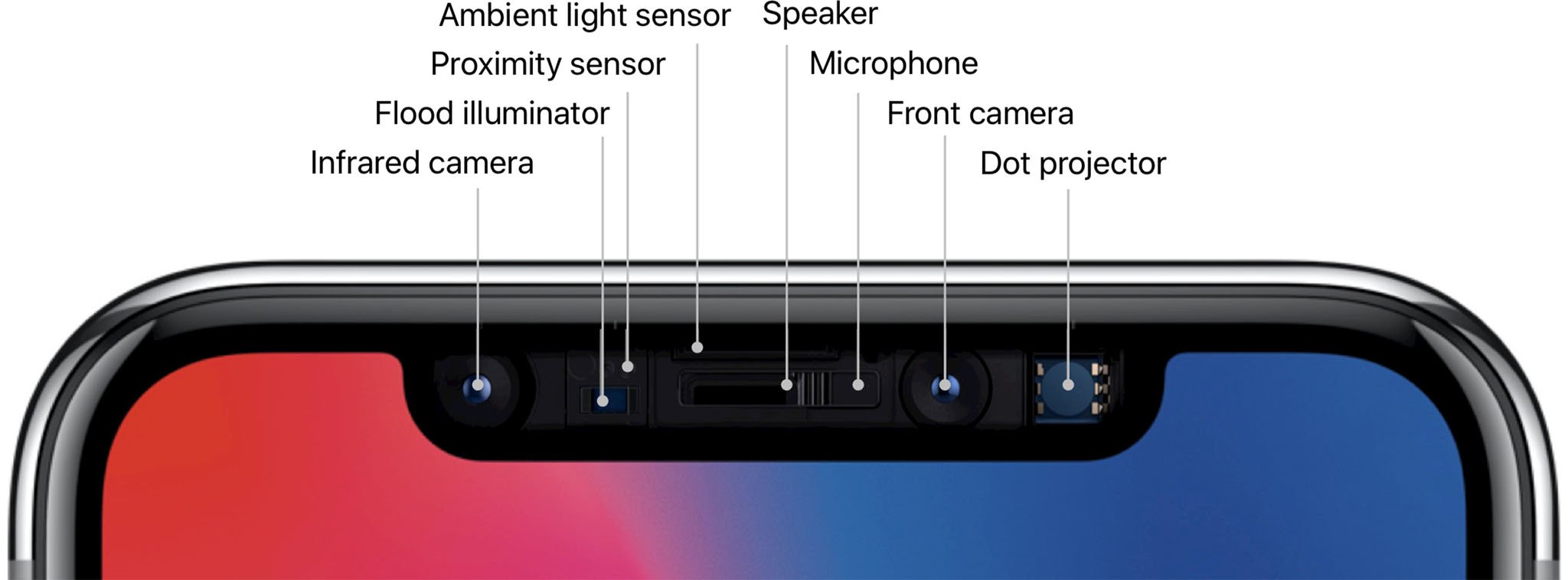
Before Face ID was released alongside iPhone X, Apple published a white paper covering its implementation and current limitations. The company followed up with a support article.
I summed them all up, and some logical extensions, in my iPhone X review:
- Face ID, as currently implemented, does not work in landscape orientation. (The camera system is optimized for portrait.)
- Face ID needs to be able to see your eyes, nose, and mouth to be able to function. If too much of that area is blocked by IR filters (like some sunglasses) or other objects (like masks), there's not enough of your face to ID. (This is like the gloved finger with Touch ID.)
- Direct sunlight on the Face ID camera can blind it, just like any camera. If you're standing with the sun directly over your shoulder, turn a bit before using Face ID. (This is like the moist finger with Touch ID.)
- If you're under the age of 13, your facial features may not yet be distinct enough for Face ID to function properly and you'll have to revert to passcode.
- Face ID can't effectively distinguish between identical twins (or triplets, etc.) If you have an identical sibling or even similar looking family member, and you want to keep them out of your iPhone X, you'll have to revert to passcode.
- If you give someone else your passcode, they can either delete and re-setup themselves on Face ID or, if they look similar to you, enter the passcode repeatedly at failure to retrain Face ID to recognize their features as well/instead.
- Unlike Touch ID, which allows for the registration of up to 5 fingers, Face ID currently only allows for one face. That means no sharing easy access with family members, friends, or colleagues.
- If, for any reason, you don't like the idea of your face being scanned, you'll have to revert to passcode or stick with a Touch ID device.
There doesn't seem to be anything shown off in video or breathless headline since that doesn't fall under any of these limitations.
Hack vs. spoof
One of the most egregious errors in reporting that's gone on around Face ID also echoes those we saw years ago with Touch ID: The conflation of hacking with spoofing.
iMore offers spot-on advice and guidance from our team of experts, with decades of Apple device experience to lean on. Learn more with iMore!
When people hear or read the word "hack", it's easy to imagine someone got into the system. In this case, the secure enclave on Apple's A11 Bionic chipset that houses the neural networks for Face ID and its data.
That absolutely has not happened. For both Face ID and Touch ID, the secure enclave remains inviolate. (That's very different from early HTC and Samsung implementations, which stored fingerprint data in world-readable directories...)
What we have seen is people try to spoof it or fool it into thinking its capturing legitimate biometric data. We saw this with Touch ID as well. We saw fingerprints being lifted and reproduced for the express purpose of fooling the sensor system. Even before biometrics, we saw this with traditional keys. People would scan and reproduce keys to get into door locks. It's exactly the type of attack you try against physical security systems.
Now we're seeing the same thing with family members, masks, and. Face ID.
Family Face ID feuds
Earlier this month, we saw two brothers post a video claiming one could unlock the Face ID system of the other. I covered it at the time:
One of the videos that got a lot of attention this weekend was made by two brothers, both of whom were eventually able to get Face ID to unlock the same iPhone X. It was revealed in a follow-up video that the first brother set up Face ID, then the second brother then tried to use it and was properly locked out. Then the second brother entered the iPhone X passcode to unlock.If someone else, including your sibling, has your iPhone X passcode, Face ID doesn't even exist. You've given them much higher access than even Face ID allows — including the ability to reset Face ID and other data on your iPhone X — and, literally, nothing else matters at that point. Keys to the castle. Time to go home.
But for Face ID in particular, there's some interesting behavior that's worth being reminded about: The neural networks that power Face ID are designed to learn and continue to match your face as you change your appearance over time. If you shave your mustache and/or beard, if you change your glasses and/or hairstyle, if you add or remove any makeup and/or facial decorations, as you put on or take off hats and/or scarves.
In the video, the second brother wasn't fooling or tricking Face ID in any way. By entering the Passcode was training it, as designed, to learn his face. By entering the Passcode multiple times, the second brother was literally telling Face ID to add his facial data to the first brother's.
More recently, we've seen younger siblings or children unlock the Face ID systems of older siblings or parents. In those cases, Passcode could also be used to train Face ID so it thinks the similar face is a new state of the registered face. In other words, it's introducing fuzziness into the system.
Even in cases where Passcode isn't being used to train a similar face, they're running into two of Apple's previously disclosed limitations:
- If you're under the age of 13, your facial features may not yet be distinct enough for Face ID to function properly and you'll have to revert to passcode.
- Face ID can't effectively distinguish between identical twins (or triplets, etc.) If you have an identical sibling or even similar looking family member, and you want to keep them out of your iPhone X, you'll have to revert to passcode.
If the facial geometry is the same and the relative is young enough that that they lack distinct facial features of their own, the chance for spoofing increases.
Mask confusion
Most recently, a Vietnamese security firm was given headlines when it claimed Face ID was successfully spoofed by dummy face. Similar to how the two brothers initially showed what looked like an immediate unlock but was subsequently disclosed as Passcode-enabled training, there turned out to be more to the mask-attack than the video first showed.
From Reuters:
Ngo Tuan Anh, Bkav's vice president, gave Reuters several demonstrations, first unlocking the phone with his face and then by using the mask. It appeared to work each time.However, he declined to register a user ID and the mask on the phone from scratch because, he said, the iPhone and mask need to be placed at very specific angles, and the mask to be refined, a process he said could take up to nine hours.
Machine Learning learns
People can shoulder-surf you (spy by looking over your shoulder) to learn your passcode. If you fall asleep they could put your finger on Touch ID. If they're a close family member or twin, they may be able to fool Face ID.

Those first two attacks are against static targets. Passcode never gets harder to spy. Touch ID is a simple data comparison. Face ID, on the other, hand learns.
Right now that learning is being tested and, in some cases, it's letting in look-almost-alikes that it should keep out. But Apple designed not only the current neural networks to adapt over time, Apple designed them to be replaceable with better neural networks over time.
From my Face ID Explainer:
Face ID keeps the original enrollment images of your face (but crops them as tightly as possible so as not to store background information). The reason for this is convenience. Apple wants to be able to update the neural network trained for Face ID without you having to re-register your face. This way, if and when the neural networks are updated, the system will automatically retrain them using the images stored in the same region of the secure enclave.
With Face ID, we don't have to wait for new hardware for it to improve. Apple can and undoubtely will improve any and every time the neural networks get updated.
Choose your own unlocks
With similar-looking relatives, concerns over false positives and unintended or unwanted access are absolutely legitimate. It can be mitigated by switching to a passcode, but Face ID is so convenient many will want to use it anyway. In those cases, it's important to remember that Face ID isn't binary. You can turn it on or off but you can also choose what Face ID can unlock even when it's on.
You can individually enable or disable Face ID for:
- iPhone unlock
- Apple Pay
- iTunes and App Store
- Safari AutoFill
- Other Apps (on an app-by-app basis)
So, if you're worried about your sibling or child unlocking your iPhone, you can turn off Face ID for that but leave it on for everything once you unlock your iPhone with Passcode. You could also leave Face ID for unlock, but turn it off for purchases if you're worried about those.
Yes, all of those introduce inconveniences, but they let you pick your own inconveniences. And if any of them are a real deal breaker, Apple also offers iPhone 8 with Touch ID, and Passcode and Password options for every iPhone.
Face to Face ID
When you tap a password manager or banking app and you watch it unlock, or you go to a website and your login suddenly fills before your eyes, it makes you forget passwords and passcodes exist. Convenience, though, is perpetually at war with security.
Face ID, like Touch ID and all biometrics, is about convenience. and identity. If you're truly concerned with security, you'll want to use a long, strong, unique password. But that's not tenable for most people. So that convenience and identity becomes vitally important.
And despite all the FUD and frantic headlines, Face ID delivers that. And, in most cases, in a far better, more transparent way than any authentication system before it.
So, by all means be informed. Read and watch everything you can. But don't let anyone scare you just so they can get views or make headlines. Try it out and decide for yourself.

Rene Ritchie is one of the most respected Apple analysts in the business, reaching a combined audience of over 40 million readers a month. His YouTube channel, Vector, has over 90 thousand subscribers and 14 million views and his podcasts, including Debug, have been downloaded over 20 million times. He also regularly co-hosts MacBreak Weekly for the TWiT network and co-hosted CES Live! and Talk Mobile. Based in Montreal, Rene is a former director of product marketing, web developer, and graphic designer. He's authored several books and appeared on numerous television and radio segments to discuss Apple and the technology industry. When not working, he likes to cook, grapple, and spend time with his friends and family.

