How to encrypt your Mac backups

Encrypting backups is a controversial subject. For some people, it's the only way to make sure their data is secure so that no one else can get to it. For others, it defeats the very purpose of backup, allowing any error or defect to render the data unrecoverable.
If saving your photos is more important to you than securing your financial data, then skip encryption. If you have more valuable information on your desk than on your backups, skip encryption. If you worry that someone else will get access to your backups and your data, then, by all means, encrypt away. Here's how.
How to encrypt a Time Machine backup
Time Machine is Apple's built-in, set-it-and-mostly-forget-it backup system for the Mac. Turn it on, and it'll make a backup of your Mac and then keep it incrementally up to date over the hours, days, and weeks that follow. While it's not encrypted by default, you can enable encryption when you set it up.
How to encrypt a clone backup
If you're using a clone backup like SuperDuper or Carbon Copy instead of Time Machine, you can also encrypt the drive. It's a two-step process to set up but, once you've got it up and running, it's just as easy to maintain as any other cloning system.
- Boot from your cloned backup drive.
- Re-install macOS to create a recovery volume on that drive.
- Turn on FileVault in System Preferences.
Unless you have a recovery volume, you won't be able to boot reliably from the clone or turn on FileVault. Once that's done, you can boot back to your primary drive once FileVault gets started; you don't have to wait for it. And once the clone backup is encrypted, you'll be able to resume your regular, iterative backup process.
- How to clone your Mac so you can use it as a backup
- How to use macOS Recovery to restore the operating system on your Mac
- How to enable FileVault on macOS
How to locally encrypt online backups
Online backup services like Backblaze and Carbonite are a different beast: You're not backing up to a drive under your physical control, where you can encrypt it yourself before transferring any data. You're backing up to someone else's servers in the cloud, typically using the encryption built into their client apps.
Some online backup services do let you set an encryption password, though, as a way of adding extra privacy and protection. However, it carries the same recovery cost as local encryption.
iMore offers spot-on advice and guidance from our team of experts, with decades of Apple device experience to lean on. Learn more with iMore!
You have the option with Backblaze to add an additional layer of privacy via a user-selected passphrase. This passphrase will be used to encrypt your private key. This passphrase is your responsibility to remember and safeguard. This is important: if you forget or lose this passphrase, there is no way that anyone, including Backblaze, can decrypt and thus restore your data. When you choose to add your own passphrase, there is no "forgot passphrase" mechanism as Backblaze does not know your passphrase.
During the initial installation, Carbonite Safe allows you to manage your own encryption key for Windows computers. If you choose to manage your own encryption key, Carbonite will prompt you to save a .PEM file which Carbonite will reference to encrypt your files before backing them up to our servers. Managing your own encryption will make it, so you are the only person capable of installing the Carbonite subscription. We recommend that you do not manage encryption keys unless you have a special need to do so, given the risk of data loss.
If you use a different online backup service, check with them about encryption passwords or encryption keys, and you should find the options you need.
Do you even encrypt your Mac backup?
If you encrypt your Mac backups, let me know your strategy — what products do you use, and how do you have your system set up?
New Mac?
Are you considering a new Mac desktop or laptop? Be sure to check out our favorite Macs of the year.
Updated November 2020: Updated local backups information.
○ Backing up: The ultimate guide
○ Best backup services and programs for your Mac
○ Best cloud service apps for your iPhone and iPad
○ How to back up your Mac
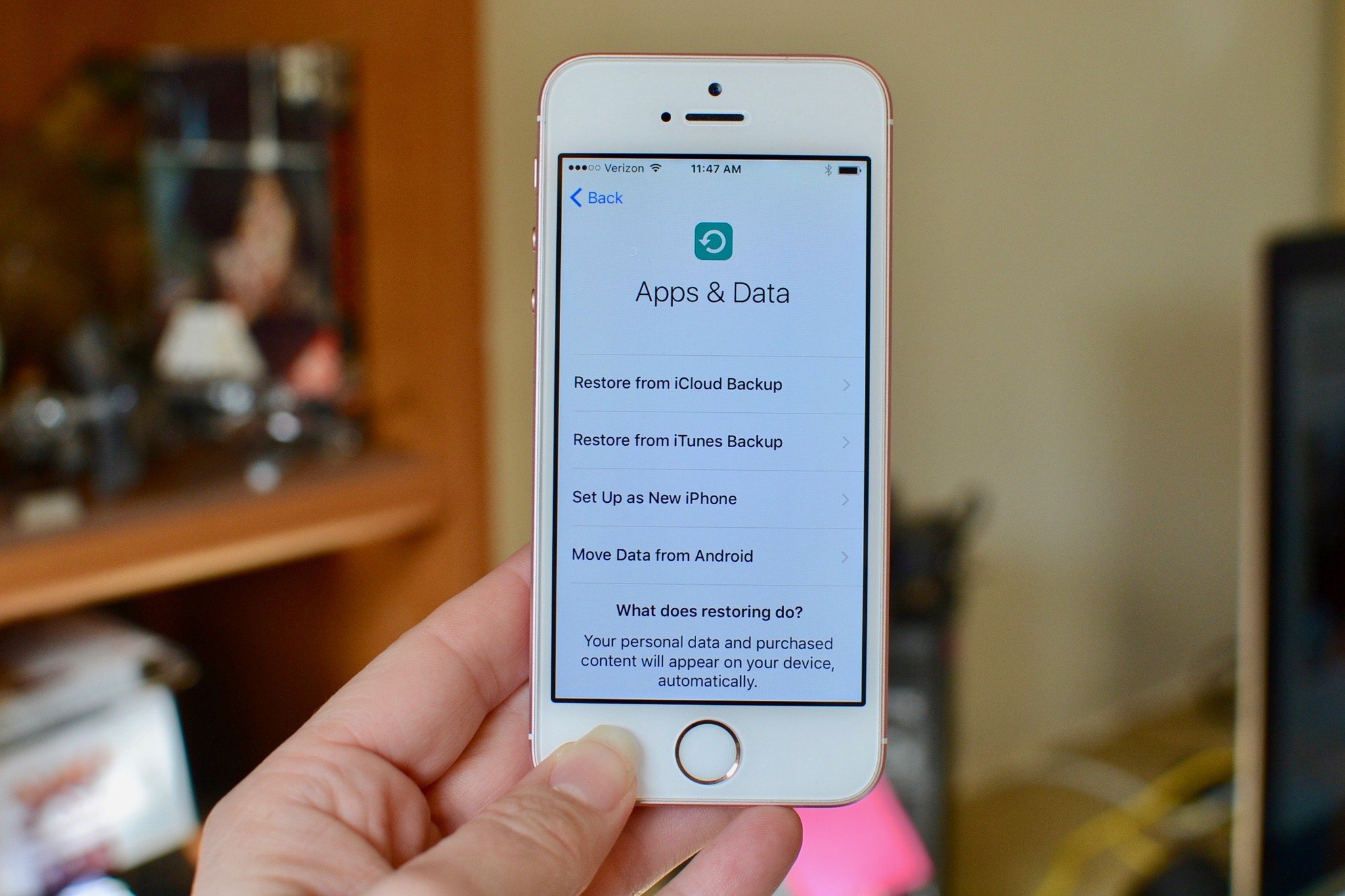
○ How to back up your iPhone and iPad
○ How to back up your Apple TV
○ How to back up your Apple Watch
○ How to restore your Mac from a backup
○ How to restore your iPhone or iPad from a backup
○ How to restore your Apple Watch from a backup
○ How to recover your files when you don't have a backup

Rene Ritchie is one of the most respected Apple analysts in the business, reaching a combined audience of over 40 million readers a month. His YouTube channel, Vector, has over 90 thousand subscribers and 14 million views and his podcasts, including Debug, have been downloaded over 20 million times. He also regularly co-hosts MacBreak Weekly for the TWiT network and co-hosted CES Live! and Talk Mobile. Based in Montreal, Rene is a former director of product marketing, web developer, and graphic designer. He's authored several books and appeared on numerous television and radio segments to discuss Apple and the technology industry. When not working, he likes to cook, grapple, and spend time with his friends and family.
