iCloud vs. iTunes backups, government demands, your privacy, and a plea for optional encryption

Apple has posted its Report on Government and Private Party Requests for Customer Information for the second half of 2016.
Apple is very seriously committed to protecting your data and we work hard to deliver the most secure hardware, software and services available. We believe our customers have a right to understand how their personal data is managed and protected. This report provides information regarding requests Apple received from government agencies and private parties from July 1 through December 31, 2016.
The TL;DR of it is that demands on the data being stored on our iPhones, iPads, and Macs are, unsurprisingly, up.
In this context, it's important to remember that while Apple protects messages and other personal data with end-to-end encryption, Apple has to turn over iCloud backups when and if required to do so by law.
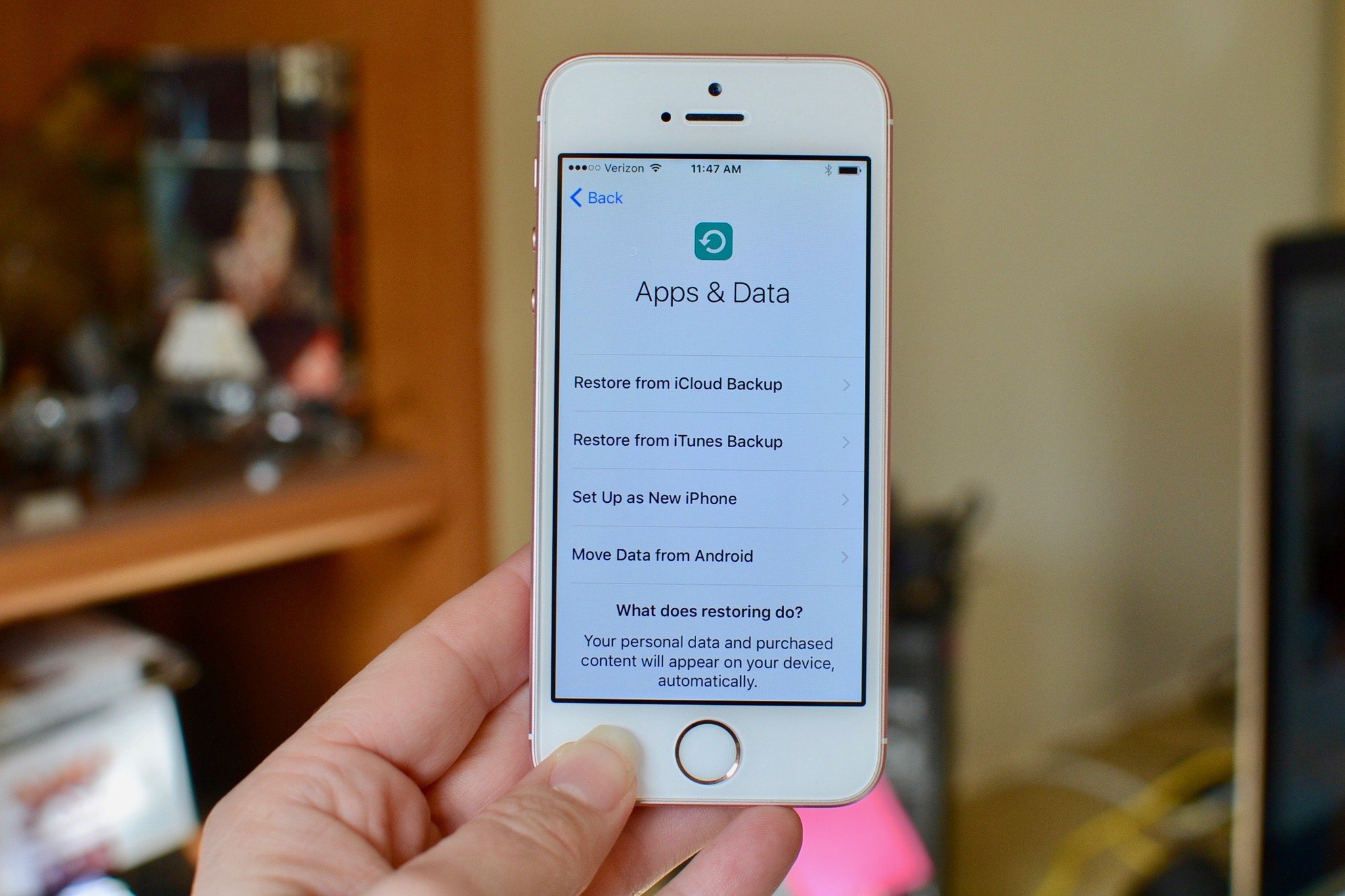
If your primary concern is convenience and data retention — you never want to lose a family photo, for example — then there's nothing new here. Keep doing what you're doing, backup to iCloud and keep unencrypted, easily recoverable backups of your Mac, unless and until your priorities change.
If your primary concern is data protection, though — you never want anyone else, including a government agency, to access your information — then skip iCloud backups and do an old-school iTunes backup and local Mac backup. And make sure it's all encrypted. Even if that means you might lose keys or not be able to recover damaged drives.
That, and join me in hoping Apple provides a way for expert users and privacy advocates to encrypt backups in such a way that absolutely no one else can ever access them. Even if it takes jumping through some initial set-up hoops, and is fail secure rather than fail safe.
That no only protects us against the abuse of privacy but hackers who get their hands on the tools used to abuse our data or the data itself once it's been demanded.
iMore offers spot-on advice and guidance from our team of experts, with decades of Apple device experience to lean on. Learn more with iMore!
○ Backing up: The ultimate guide
○ Best backup services and programs for your Mac
○ Best cloud service apps for your iPhone and iPad
○ How to back up your Mac
○ How to back up your iPhone and iPad
○ How to back up your Apple TV
○ How to back up your Apple Watch
○ How to restore your Mac from a backup
○ How to restore your iPhone or iPad from a backup
○ How to restore your Apple Watch from a backup
○ How to recover your files when you don't have a backup

Rene Ritchie is one of the most respected Apple analysts in the business, reaching a combined audience of over 40 million readers a month. His YouTube channel, Vector, has over 90 thousand subscribers and 14 million views and his podcasts, including Debug, have been downloaded over 20 million times. He also regularly co-hosts MacBreak Weekly for the TWiT network and co-hosted CES Live! and Talk Mobile. Based in Montreal, Rene is a former director of product marketing, web developer, and graphic designer. He's authored several books and appeared on numerous television and radio segments to discuss Apple and the technology industry. When not working, he likes to cook, grapple, and spend time with his friends and family.
