
Apple's iPhone 18 chip technology might have been announced as TSMC touts advanced 1.6nm fabrication
TSMC has announced that it is working on new chip technology for 2026, and it could debut in Apple's iPhone 18.
iMore offers spot-on advice and guidance from our team of experts, with decades of Apple device experience to lean on. Learn more with iMore!

By Oliver Haslam published
Congo has accused Apple of using blood minerals and has demanded a response from CEO Tim Cook.

By Stephen Warwick published
iPhone customers are being told by Apple that their trade-ins have been canceled by a glitch email.

By Oliver Haslam published
Apple is working on a new iOS 18 update laden with AI features and now it's made a number of LLMs available online.

By John-Anthony Disotto last updated
The best MagSafe charging stand is the perfect way to take advantage of StandBy mode in iOS 17. Here are our favorites.

By Stephen Warwick published
iPhone customers are being told by Apple that their trade-ins have been canceled by a glitch email.

By Stephen Warwick last updated
The iPhone 16 is expected to arrive in September 2024 and it could be one of the biggest upgrades in some time.
By Oliver Haslam last updated
The iPhone 16 Pro is expected to come with a few changes compared to the model you're already carrying.

By Oliver Haslam published
Someone found a way to get the EU's DMA features like third-party app stores and more, but the workaround probably isn't worth the hassle.

By Oliver Haslam last updated
It's inevitable that the iPad Air lineup will get a refreshed model and here's what we've been hearing so far.

By Oliver Haslam published
This new iPad stand is adjustable, has a USB-C hub included, and looks great to boot.

By Oliver Haslam published
Rumors of a new iPad Air 6 with a mini-LED display were wrong, but we'll see a new 12.9-inch iPad instead, analyst says.

By Daryl Baxter published
Apple is reportedly planning to bring its Calculator app to iPadOS 18, ending 14 years of wishing from users.

By Oliver Haslam published
Apple isn't expected to update its Mac mini or Mac Pro lineups with M3 chips, leaving buyers to wait for M4 versions instead.

By Connor Jewiss published
According to a new report, the upcoming macOS 15 update is set to include a revamped and smarter Calculator app that looks like the one on iOS.

By Stephen Warwick last updated
With the advent of Apple silicon, gaming on Mac is better than ever. But what's the best gaming MacBook you can buy right now?

By Stephen Warwick published
2024 could herald the first wave of M4 Macs, what do we know about the next generation of Apple silicon?

By Karen S Freeman last updated
Apple makes some fantastic bands for the Apple Watch, that's for sure. But you can expand your band wardrobe with some incredible third-party options. Here are some of our favorites.

By Karen S Freeman last updated
Ultimate bands for the ultimate watch.

By James Bentley published
Apple Watch Ultra 2 is now available refurbished at the Apple store, which means you can get a restored Apple Watch with official parts for cheaper.

By Andrew Williams published
Fallout 4 may never have been ported to macOS, but there are multiple ways to play it on Mac.

By Daryl Baxter published
Quick Tips Thanks to this handy trick in Delta for iPhone, you can launch your retro games directly from the Home Screen.

By John-Anthony Disotto published
Quick Tips You can search using Spotlight directly from your iPhone's Lock Screen — I wish I'd known all this time.

By James Bentley last updated
Is AirDrop not working on your iPhone? Here are a few things you can try to get Apple's file transfer feature to work again.

By Andrew Williams published
Fallout 4 may never have been ported to macOS, but there are multiple ways to play it on Mac.

By John-Anthony Disotto last updated
You can play retro games with Delta Game Emulator for iPhone. Here's everything you need to know to add games, play games, and use the app everyone's talking about.

By James Bentley published
With Apple allowing game emulation on its app store, users have had a great week of video games, despite developers worrying about Apple’s guidelines.

By James Bentley published
PPSSPP, a PSP emulator for iPhone, is currently in the works but Apple’s unclearness around its own rules leaves the developer unsure of if it will launch.

By James Bentley published
The Lofree Dot Foundation is a gorgeous mechanical keyboard that takes its looks from makeup. Our review:

By Gerald Lynch published
The Satechi Thunderbolt 4 Slim Pro Hub is excellent — if all you need is more Thunderbolt ports for your Mac and practically nothing else.

By John-Anthony Disotto published
The BenQ beCreatus DP1310 is the perfect dock for Mac users who play games on console. With just one click you can jump between USB-C and HDMI 2.1.

By Alex Blake published
Stage View adds previews to apps and windows in the Stage Manager sidebar. Is it worth your cash?

By Tammy Rogers published
The Geekom A7 is a powerful, tiny, and very well-priced mini PC — but should you choose one over the Mac mini?

By Alex Blake published
The Logitech Signature Slim K950 is a more affordable version of the MX Keys S, with a similar typing feel but without a few nice-to-haves.

By Stephen Warwick published
President Biden has signed the TikTok ban into law, giving owner ByteDance 9 months to sell the company.

By Matt Evans published
How do Apple Fitness Plus’ exercise bike classes compare to the real thing? We look at the benefits and disadvantages.

By Becca Caddy published
App of the day The Tyme 3 iPhone and Mac app is for individuals and teams, and it works seamlessly when you're on the move.
By Becca Caddy published
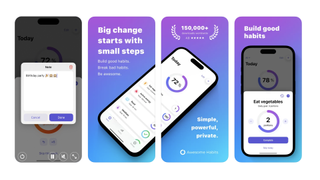
App of the day Awesome Habits isn't just another habit tracking app, it's perfect if you're overwhelmed by choice and want a straightforward option.